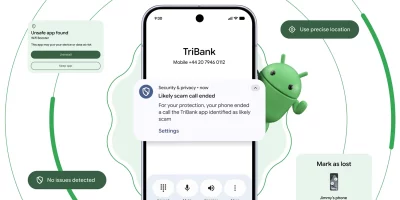
Android pushes new scam, theft, and AI protections in 2026 update wave
Phone scammers spoofing bank caller IDs have driven an estimated $980 million in annual losses worldwide, according to Europol. Android’s 2026 security roadmap takes …

iOS 26.5 is out, bringing encrypted RCS messaging to iPhone and Android users
Apple is bringing long-awaited end-to-end encryption to Rich Communication Services (RCS) messaging between iPhone and Android users in iOS 26.5. The feature is launching in …

Google is turning Android Studio into a policy watchdog
Google has expanded Play Policy Insights in Android Studio to help developers catch policy issues while coding, including warnings for common problems such as missing login …

Mental health apps are collecting more than emotional conversations
People use mental health apps to talk about depression, trauma and suicidal thoughts in moments they may not share with anyone else. Many users likely assume those …

Product showcase: NetGuard open-source firewall for Android
NetGuard is a free, open-source firewall for Android phones and tablets that provides users with a simple way to block internet access. Android does not allow VPN services to …

CallPhantom Android scam reached 7.3 million downloads on Google Play
Scams targeting Android users in India and across the Asia-Pacific region have grown around a long-standing curiosity gap: the desire to look up call records tied to a phone …

Chrome on Android can now hide your exact location from websites
Google is improving location privacy features that give users more control over sharing their location. On Chrome for Android, users can now choose to share their approximate …

Google expands Android Binary Transparency to counter supply chain attacks
Supply chain attacks on mobile software have grown alongside the expanding role of phones in daily life, from payments to government IDs to AI features. Google is responding …

Google to pay up to $1.5 million for zero-click Pixel Titan M exploits
Google has revised its Android and Chrome Vulnerability Reward Programs (VRPs), which pay security researchers to report vulnerabilities in Android, Google hardware, and the …

Your work apps are quietly handing 19 data points to someone
Office work in 2026 runs through a stack of mobile apps that sit on the same phones people use for banking, messaging family, and tracking their location. Ten of the most …

Product showcase: SimpleX Chat removes user identifiers from messaging
SimpleX Chat is a free, private, open-source messenger that uses encryption and does not require user identifiers. It is available on mobile and desktop platforms, including …

A study of 1,000 Android apps finds a privacy policy logging gap
Android developers write log statements for the same reasons they always have: debugging crashes, tracing performance issues, and understanding how features behave in …
Featured news
Resources
Don't miss
- Sandyaa: Open-source autonomous security bug hunter
- The hidden risk of non-human identities in AI adoption
- Researchers open-source a Wi-Fi cyber range for security training
- Android pushes new scam, theft, and AI protections in 2026 update wave
- Microsoft May 2026 Patch Tuesday: Many fixes, but no zero-days