
LiteLLM vulnerability under active attack, CISA warns (CVE-2026-42271)
A command injection vulnerability (CVE-2026-42271) in BerryAI’s LiteLLM open-source AI gateway is being exploited by attackers, the US Cybersecurity and Infrastructure …
Treating AI agents like service accounts for federated query security
In this interview with Help Net Security, Paras Malhotra, CISO at Starburst, explains how the company handles data governance across federated query environments. Topics …
The security questions around Chinese AI coding models in U.S. software
Software developers across the United States are using AI models built in China to write, debug, and review code, drawn by prices below those of American alternatives. These …

Autonomous AI-driven worm can reason its way through corporate networks
Researchers at the University of Toronto, the Vector Institute, and the University of Cambridge have built and tested a proof-of-concept AI-driven worm that does not operate …

AI red teaming agents change how LLMs get tested
Adversarial probing of LLMs has piled up a sprawling toolkit over the past three years. Attack techniques with names like Tree of Attacks with Pruning, Crescendo, and Skeleton …
When your AI assistant has the keys to production
Large language models in operational roles query telemetry, propose configuration changes, and in some deployments execute those changes against live infrastructure. Ticket …

The AI backdoor your security stack is not built to see
Enterprises deploying LLMs have spent the past two years building defenses around a reasonable assumption: malicious behavior leaves a trace in the input. Scan for suspicious …
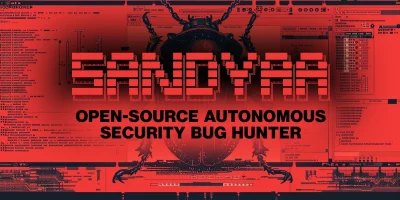
Sandyaa: Open-source autonomous security bug hunter
Source code auditing has traditionally relied on static analyzers that flag long lists of potential issues, leaving engineers to sort bugs from noise. A new open-source …
HEIDI: Free IDE security plugin for open-source vulnerability checks
Open-source dependencies make up a large percentage of the code in production applications, and most vulnerability checks still run late in the pipeline, inside CI/CD systems …

Cutting the cost of SIEM rule conversion
You inherit two thousand detection rules from an acquisition. They are written for a platform your company does not use. Your senior detection engineer estimates six months to …

Unpatched flaws turn Ollama’s auto-updater into a persistent RCE vector, researchers say
Researchers at Striga have disclosed two vulnerabilities (CVE-2026-42248, CVE-2026-42249) in Ollama’s Windows auto-updater that, when chained together, may allow an …
Can your coding style predict whether your code is vulnerable?
Developers leave fingerprints in the code they write. Naming choices, indentation patterns, preferred APIs, and the way someone structures a loop or handles a pointer all …
Featured news
Resources
Don't miss
- LiteLLM vulnerability under active attack, CISA warns (CVE-2026-42271)
- The architecture of subtraction: Why it’s time to erase the roads, not just map the traffic
- Treating AI agents like service accounts for federated query security
- Malware ships with bugs that defenders could use against it
- Qilin ransomware affiliate exploited Check Point VPN zero-day (CVE-2026-50751)