monitoring

The Exchange Online security controls organizations keep getting wrong
In this Help Net Security interview, Scott Schnoll, Microsoft MVP for Exchange, breaks down the Shared Responsibility Model, where Microsoft secures the cloud while …
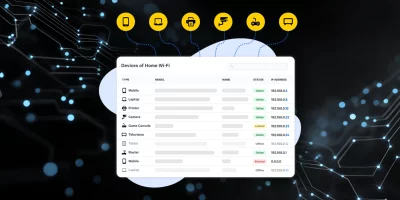
Product showcase: Fing Desktop puts network visibility on your screen
Phones, laptops, smart TVs, cameras, and smart home equipment all use the same network. Knowing what’s connected helps users manage performance and security. Fing Desktop …

Uptime Kuma: Open-source monitoring tool
Service availability monitoring remains a daily operational requirement across IT teams, SaaS providers, and internal infrastructure groups. Many environments rely on …

Security leaders push for continuous controls as audits stay manual
Security teams say they want real-time insight into controls, but still rely on periodic checks that trail daily operations. New RegScale research shows how wide that gap …
Anubis: Open-source web AI firewall to protect from scraper bots
Anubis is an open-source tool designed to protect websites from automated scraping and abusive traffic by adding computational friction before a request is served. Maintained …
Zabbix: Open-source IT and OT observability solution
Zabbix is an open source monitoring platform designed to track the availability, performance, and integrity of IT environments. It monitors networks along with servers, …
Prometheus: Open-source metrics and monitoring systems and services
Prometheus is an open-source monitoring and alerting system built for environments where services change often and failures can spread fast. For security teams and DevOps …

The tech that turns supply chains from brittle to unbreakable
In this Help Net Security interview, Sev Kelian, CISO and VP of Security at Tecsys, discusses how organizations can strengthen supply chain resilience through a more unified …

AI can flag the risk, but only humans can close the loop
In this Help Net Security interview, Dilek Çilingir, Global Forensic & Integrity Services Leader at EY, discusses how AI is transforming third-party assessments and due …
Faster LLM tool routing comes with new security considerations
Large language models depend on outside tools to perform real-world tasks, but connecting them to those tools often slows them down or causes failures. A new study from the …

Everyone wants AI, but few are ready to defend it
The rush to deploy AI is reshaping how companies think about risk, according to Cisco. A global study finds that while most organizations are moving quickly to adopt AI, many …
Maltrail: Open-source malicious traffic detection system
Maltrail is an open-source network traffic detection system designed to spot malicious or suspicious activity. It works by checking traffic against publicly available …
Featured news
Resources
Don't miss
- Cisco patches another actively exploited SD-WAN zero-day (CVE-2026-20182)
- Unpatched Microsoft Exchange Server vulnerability exploited (CVE-2026-42897)
- Deepfake detection is losing ground to generative models
- Fragnesia: New Linux kernel LPE bug was spawned by Dirty Frag patch (CVE-2026-46300)
- Vector embedding security gap exposes enterprise AI pipelines