
Russian hackers are exploiting recently patched Microsoft Office vulnerability (CVE-2026-21509)
Russian state-sponsored hackers Fancy Bear (aka APT 28) are exploiting CVE-2026-21509, a Microsoft Office vulnerability for which Microsoft released an emergency fix last …

Download: Tines Voice of Security 2026 report
Security teams everywhere are adopting AI. Yet manual work persists, workloads are rising, and burnout continues to climb. To understand what’s really changing, Tines surveyed …
Notepad++ supply chain attack: Researchers reveal details, IoCs, targets
Rapid7 researchers have attributed the recent hijacking of the Notepad++ update mechanism to Lotus Blossom (aka Billbug), a Chinese state-sponsored group known for targeting …

Sandisk brings SPRandom to open source for large SSD testing
Enterprise storage environments already run long qualification cycles as solid-state drive capacities rise and validation teams try to mirror production workloads. …
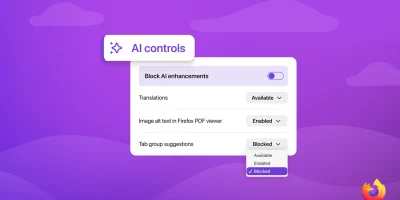
Firefox to let users manage and block AI features
Mozilla will add a set of controls in Firefox that let users manage and block GenAI features in the desktop browser. The controls will be included in Firefox version 148 on …
OpenAI releases Codex macOS app for agent-based software development
OpenAI has launched the new Codex app for macOS, a dedicated workspace for managing multiple AI coding agents in parallel. The app is designed to help developers reduce …

Why boards must prioritize non-human identity governance
Boards of Directors (BoDs) do three things exceptionally well when cyber is framed correctly. They set risk appetite, they allocate capital, and they demand evidence that the …

Open-source attacks move through normal development workflows
Software development relies on a steady flow of third-party code, automated updates, and fast release cycles. That environment has made the software supply chain a routine …
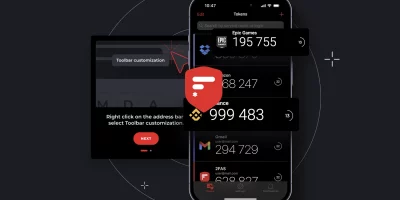
Product showcase: 2FAS Auth – Free, open-source 2FA for iOS
Online accounts usually rely on a password, but passwords alone can be weak if they’re reused, easily guessed, or stolen. Two-factor authentication (2FA) adds a second layer …

Cybersecurity jobs available right now: February 3, 2026
Application Security Engineer Liebherr Group | Germany | Hybrid – View job details As an Application Security Engineer, you will As an Application Security Engineer, you …

ShinyHunters flip the script on MFA in new data theft attacks
Multi-factor authentication (MFA) is supposed to defend against phishing attacks, but threat actors operating under the ShinyHunters banner are using it as a pretext in …

How state-sponsored attackers hijacked Notepad++ updates
UPDATE: Notepad++ supply chain attack: Researchers reveal details, IoCs, targets Suspected Chinese state-sponsored attackers hijacked the Notepad++ update mechanism by …
Featured news
Resources
Don't miss
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)
- Acrobat Reader zero-day exploited in the wild for many months
- AI agent intent is a starting point, not a security strategy
- Asqav: Open-source SDK for AI agent governance
- BlueHammer: Windows zero-day exploit leaked