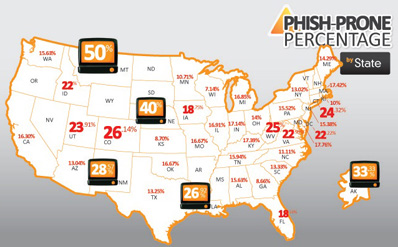
Cybercrime statistics show widespread phishing problem
The top five industries vulnerable to cybercrime include travel, education, financial services, government services and IT services, according to KnowBe4.
Using the Inc.com website to obtain domain names and a free data-gathering service to find publicly available email addresses, KnowBe4 sent out a simulated phishing email to employees at more than 3,500 companies. Individuals who clicked the link were directed to a landing page that informed them they had just taken part in phishing research.
The emails were successfully delivered to about 29,000 recipients at 3,037 businesses; and in nearly 500 of those companies, one or more employees clicked the link. Because of the potential for Internet security breaches among these businesses, KnowBe4 dubbed them the FAIL500.
“Any business that provides access to email or access to its networks via the Internet is only as safe from cybercrime to the degree that its employees are trained to avoid phishing emails and other cyberheist schemes. The more employees within an organization that use email or go online, the greater the risk of exposure to cybercrime,” said KnowBe4 CEO Stu Sjouwerman.
“Our cybercrime statistics should serve as a wake-up call to SMEs nationwide,” noted Sjouwerman. “Not only are these businesses at risk for financial loss through a cyberheist, but their susceptibility to phishing tactics could compromise sensitive customer data such as credit card, bank account and social security numbers.”
Sjouwerman cites a “false sense of security” as the primary reason companies are vulnerable to cybercrime. “Most people assume that antivirus software and an in-house IT team provide sufficient data security. But considering that IT is among the most phishing-prone industries, it’s clear that’s a very dangerous assumption to make.”
Cybercriminals have become very sophisticated in their tactics, and they often target businesses through official-looking emails that appear to be sent by government agencies, business partners or even company executives.
Many of the top phishing-prone industries are regulated and subject to compliance rules, so well-meaning employees can be tricked into clicking a link if they believe an email was sent by a government or law enforcement agency, or by someone they know and trust. And with just one click, malware can be instantly uploaded to a system – bypassing both antivirus software and IT firewalls. A cyberheist can be underway within minutes.