Data breaches hit all-time record high, increase 40% in 2016
The number of U.S. data breaches tracked in 2016 hit an all-time record high of 1,093, according to a new report by the Identity Theft Resource Center (ITRC) and CyberScout. This represents a substantial hike of 40 percent over the near record high of 780 reported in 2015.

This raises the question: are there actually more breaches or is it because more states are making this information publicly available?
“For the past 10 years, the ITRC has been aware of the under-reporting of data breach incidents on the national level and the need for more state or federal agencies to make breach notifications more publicly available. This year we have seen a number of states take this step by making data breach notifications public on their websites. The ITRC Data Breach Report 2016 now includes information from more than a dozen state agencies,” said Eva Velasquez, President and CEO, ITRC.
Since 2005, the ITRC has been identifying data breaches in five industry sectors. In 2016, the business sector again topped the list in the number of data breach incidents, with 494 reported, representing 45.2 percent of the overall number of breaches. This was followed by the healthcare/medical industry (377 incidents), representing 34.5 percent of the overall total. The education sector (98) followed at 9.0 percent, the government/military (72) at 6.6 percent and the banking/credit /financial sector (52) at 4.8 percent.
Leading types of data breaches
In 2007, the ITRC began adding categories to identify data breach incidents by the “type of occurrence.” For the eighth consecutive year, hacking/skimming/phishing attacks were the leading cause of data breach incidents, accounting for 55.5 percent of the overall number of breaches, which is an increase of 17.7 percent over 2015 figures. Of these, many were a result of CEO spear phishing efforts (also known as business email compromise schemes) in which highly sensitive data, typically information required for state and federal tax filings, was exposed. As early as February, the IRS had already seen a 400 percent surge in this type of activity prompting both consumer and industry alerts addressing this issue.
Breaches involving accidental email/internet exposure of information was the second most common type of breach incident at 9.2 percent of the overall number of breaches followed by employee error1 at 8.7 percent. With the exception of hacking, all other categories reflected decreases from 2015 figures.
“For businesses of all sizes, data breaches hit close to home, thanks to a significant rise in CEO spear phishing and ransomware attacks. With the click of a mouse by a naïve employee, companies lose control over their customer, employee and business data. In an age of an unprecedented threat, business leaders need to mitigate risk by developing C-suite strategies and plans for data breach prevention, protection and resolution,” said Matt Cullina, CEO of CyberScout and Vice Chair of ITRC’s Board of Directors.

Exposure of personal information
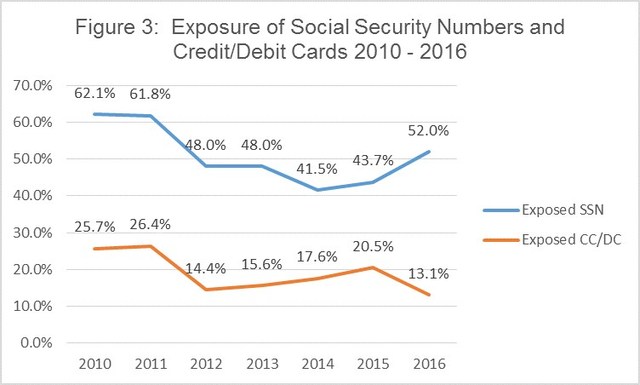
Since 2010, the ITRC has been tracking breaches involving Social Security numbers (SSNs) and credit card/debit card numbers. Exposure of SSNs was evidenced in 52.0 percent of the overall number of breaches in 2016, representing an increase of 8.2 percent over 2015 figures.
Exposure of records involving credit/debit cards at 13.1 percent, reflects a decrease of 7.4 percent from 2015. With that said, it is important to remember that most data breach notifications or media reports do not include the type of information exposed. The spike in SSN exposures is in clear alignment with the surge of CEO spear phishing attacks, which target this type of information.
“Consumers must become better informed as to the risks inherent in this dangerous digital world, be more alert to the signs of individual compromise and know what to do to contain and reverse the damage or take advantage of identity theft protection services offered by their insurers, employers or financial services firms,” said Adam Levin, Chairman of CyberScout.
Number of exposed records
Regarding the reporting of the known number of records exposed, half (50.7 percent) of the overall number of breach notifications did not include this information. However, due to the mandatory reporting requirement for healthcare industry breaches affecting 500 or more individuals, 84 percent of the healthcare breaches publicly stated the number of records exposed.
It should also be noted that several large scale breaches in 2016— which only involved usernames, passwords, or emails— while included on the list, did not specify the vast number of records exposed because this type of information does not typically trigger most data breach notification laws.
“The ITRC has always been dedicated to portraying an accurate picture of what is happening with data breaches in the United States. As such, it makes every effort to update categories and methodologies to better capture patterns and trends,” said Karen Barney, ITRC Director of Research and Publications. “Going forward, we hope both businesses and government reporting organizations will continue to be more transparent about the details of breached information so we may better inform consumers on the types of risks involved with the exposure of various types of personal information.”