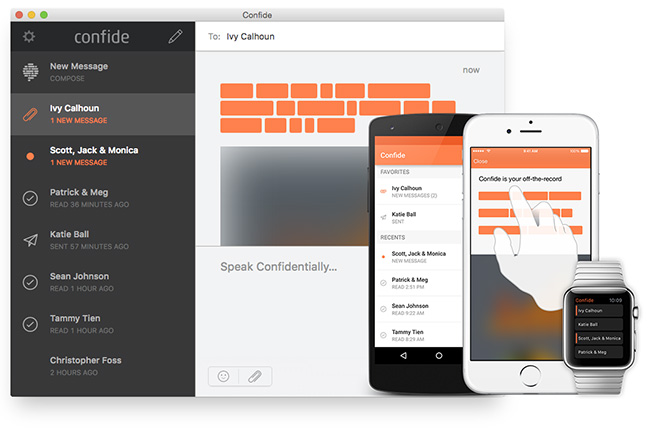
Encrypted messaging app Confide suffers from many security issues
Confide, the encrypted instant messaging application with a self-destructing messaging system that has become popular with White House staffers, is not so secure after all.
IOActive released today the results of the company’s recent research into the app, and noted that they found several issues which could be exploited by an attacker to impersonate another user by hijacking their account session or by guessing their password, learn the contact details of all or specific Confide users, become an intermediary in a conversation and decrypt messages, and alter the contents of a message or attachment in transit without first decrypting it.
That was all possible because, among other things:
- The application’s notification system did not require a valid SSL server certificate to communicate
- The user interface made no indication when unencrypted messages were received
- The app failed to use authenticated encryption (giving Confide the ability to alter messages in-transit)
- It allowed an attacker to enumerate all Confide user accounts and failed to prevent brute-force attacks on user account passwords
- The application’s website was vulnerable to an arbitrary URL redirection, which could facilitate social engineering attacks against its users.
The researchers disclosed the flaws to the company behind the app, and Confide apparently fixed all the critical issues in the newest versions of the products (Windows client, Android app).
But on the same day, Quarkslab researchers came out with the results of their own testing of the security of the app, including version 1.4.3 of the Windows version (the latest one out).
They say that Confide can read all the messages that pass through its servers, as it can create a new set of encryption keys for users without them being notified, and use those keys to decrypt users’ messages.
Also, that anyone who is able to inject a public key in the TLS session can read all messages without having the user knowing it.
“Currently, at least Confide or attackers who compromised the Confide servers are technically able to do so by design,” they noted. “Without access to the Confide servers, the attack would require to defeat the TLS layer and the HTTP public key pinning.”
Finally, they also say that the screenshot prevention and message deletion security features can be foiled, and promised to reveal how in a future post.
All in all, the researchers say, users should not consider the messaging app to be completely secure, and should decide whether they can risk using it until the company solves the issues.