Review: Cato Cloud
The Innovation Sandbox at the RSA Conference is one of the show’s events that I never miss. Back in February, I watched through the demos and live presentations of Cato Networks, one of the event’s ten finalists. Even in a room packed with innovative technologies, their solution – described as “network + security as a service” – definitely stood out.
Cato Cloud is a custom-built, SLA-backed backbone that provides global organizations a one-stop solution for interconnectivity, security and policy enforcement.
Addressing the challenges
Cato Networks was founded by guys who, back in the day, started Check Point Software. The idea behind the company’s flagship solution is based on the belief that network security appliances and Wide Area Network (WAN) offerings are not optimized for securing the currently dissolving network perimeter.
Some of the issues with WANs include extensive MPLS (Multiprotocol Label Switching) costs, roll-out complexities, and relative unpreparedness for everything cloud- and mobile-related. Network security appliances, on the other hand, can be costly, somewhat problematic to deploy and manage (especially for a global organization with large number of branches), and it seems there’s always a need to chain multiple appliances to address the complexity of newly discovered threats.
The Cato Cloud is a global network of physical Points-of-Presence (PoPs) that are interconnected into a backbone consisting of multiple Tier-1 carriers with multi-gigabit links. All the traffic in the backbone is encrypted and all the PoPs are built with redundancy and high availability in mind. The system doesn’t rely on third party technologies and its purpose is to provide a completely integrated network carrying both WAN and Internet traffic. At the same time, the solution incorporates top-grade security technologies, as well as a unified policy that can be enforced across the organization.
Connecting to the network
Connecting your organization to the Cato Cloud is a rather straightforward process. Depending on your preferences and potential dependencies on existing security hardware, the connection can be established in one of two ways. If you depend on the exisiting firewall, UTM or router, connecting to the nearest Cato PoP should be done via an IPSec tunnel. The nearest PoP is equal to the PoP with the lowest latency.
As you will see later on in the review, one of the ideas behind Cato’s solution is to give organizations the possibility to eliminate a number of security mechanisms already deployed on their network.
Cato Networks will provide you with the Cato Socket, a small tunnelling device for every location you want to connect to the Cato Cloud. It is a simple device that is easy to install (it provisions itself) and its purpose is to send the encrypted traffic to the nearest PoP.
The device itself purposely doesn’t have any additional “brain power,” making it much more effective and capable of fast transmission of large quantities of data. For customers using Amazon AWS or Microsoft Azure, a virtual instance of Cato Socket is available.
At the moment, there are 34 PoPs spread evenly across the globe – 12 are located in North America, 8 in Europe, 11 in Asia, and one in Israel, South Africa and Brasil. According to the company, the latency in every connection between the branch of your organization and the nearest PoP should be under 25ms. When your data is travelling between two PoPs, it will be encrypted on a single carrier. As the product uses its custom-made networking and security stack, the whole process of routing can be controlled to provide optimum performance.
The security dashboard
Cato Cloud’s security dashboard is divided into four sections. WAN firewall is there to set up accepted connections in the company WAN. It is easy to create a custom set of rules for every object inside your network – groups, sites, hosts, VPN users and networks. With just a click or two, you can select any object and apply access rules to it. There is also an extensive list of constraints (222 to be precise) that can be added to any rule to make it more efficient: for example, you can choose specific protocols or services, set time frames during which some options cannot be used, or define bandwidth limits.
When any of the rules are triggered, the system will act accordingly and administrators will be alerted both via the analytics section (more on it below), and via email.
Cato Cloud’s Internet firewall acts the same as its WAN counterpart. It has the same style of picker, but also features an additional pre-populated list of web applications and categories on which you can base blocking. You can also do URL filtering with custom rules, which include the predefined categories, as well as manual TLDs and FQDNs. Every category and custom rule has four action levels you can set – Allow, Block, Monitor, and Prompt.
Cato Cloud also incorporates Anti-malware and IPS functionalities, effectively making some other software or hardware solutions you are currently using obsolete. The signatures and threats are regulary updated, so all users throghout the organization will automatically be protected from any new malware or exploit.
Securing the mobile workforce
Having complete control over networking and Internet access really helps when it comes to managing the mobile workforce. Cato Cloud tackles this hot issue by having custom applications for all desktop operating systems (Windows, macOS, Linux), as well as popular mobile platforms (iOS, Android). Any user added into the dashboard will get credentials and will be able to install Cato software on the devices she prefers. These VPN installations will always connect to the nearest PoP. The speeds shown in my tests were impressive.
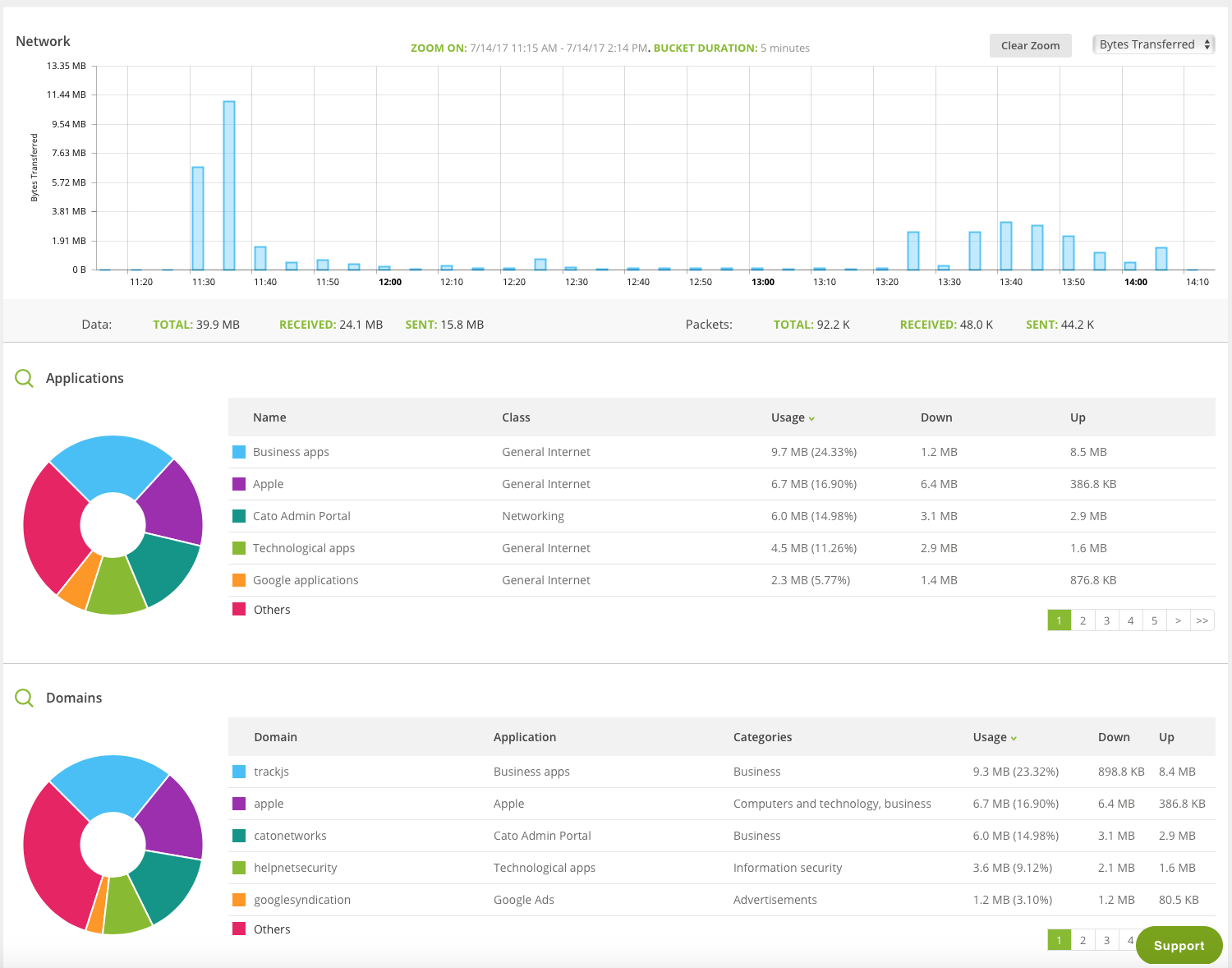
As soon as the user connects to the network with the device, a new icon appears in the network topology screen of the management dashboard. Clicking on it (or choosing the user via the left side menu) will show a plethora of information on both the current usage and historical data. What I absolutely loved about this is the sheer magnitude of data collected, as well as the superb presentation of it.
Through all the product testings I’ve performed in the past twenty years, I often noted a discrepancy between the quality of the product and the quality of its user interface, especially since dashboards started being moved into the web browser. Fortunately, Cato Networks excels on this front – the UI is straightforward and logical, and it worked fast and flawlessly on multiple operating systems and browsers.
Additional analytics
I mentioned user analytics previously in this article, but you can also run similar graphical and textual representation for your branches (i.e.”sites”), apps, domains and URL categories. From the security perspective, there are two standalone screens offering administrators a current view of potential threats within their organization.
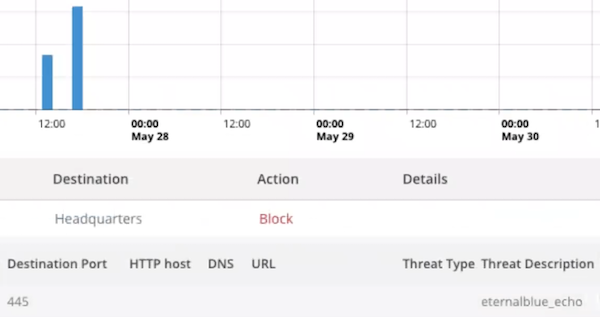
Based on the setup of the security levels, admins can dig deeper in every security event generated by the system, and can easily analyze the data according to the type of threat, actions, destination, and user account. If the IPS detects any malware or attack, the same list of details will be provided for the threat in question.
Pricing
The pricing structure for this type of solution turns out to be simple: the only factor used is the bandwidth. All other network and security mechanisms, both sofware ones built into the platform as well as the hardware Cato Sockets, are included in the price.
Final thoughts
Cato Cloud is an innovative platform that solves a number of pressing issues global companies have these days. The idea of building everything from ground-up is terrific and it is definitely a must for this type of distruptive technology. Every aspect of the Cato Cloud excells, offering organizations a powerful networking and security infrastructure that is easy to implement and manage.