Enterprise container security: There’s room for improvement
With companies such as Facebook, Netflix and Google heralding the use of containers for their agility, portability, and cost benefits – enterprises are following suit. But the introduction of new processes and changes to infrastructure require a significant shift in focus.
To learn the current state of container security in the enterprise, Aqua Security surveyed 512 individuals meeting the criteria of using containers in development or production today, or planning to use them in the near future.
Key insights
- 50% of respondents have container applications in production
- 80% see room for improvement for handling security in the container era
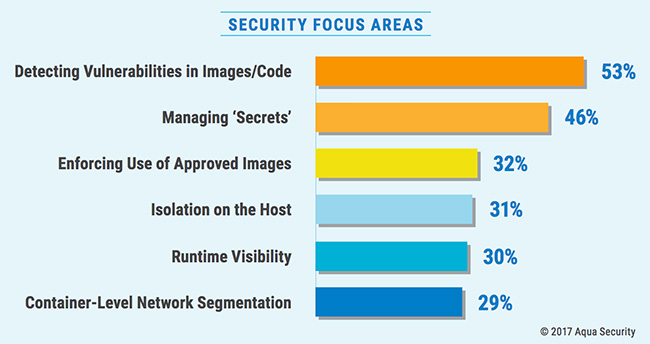
- 53% overall rank vulnerabilities in images and code as a top security focus area
- For those running multiple container apps in production, managing ‘secrets’ is their main focus
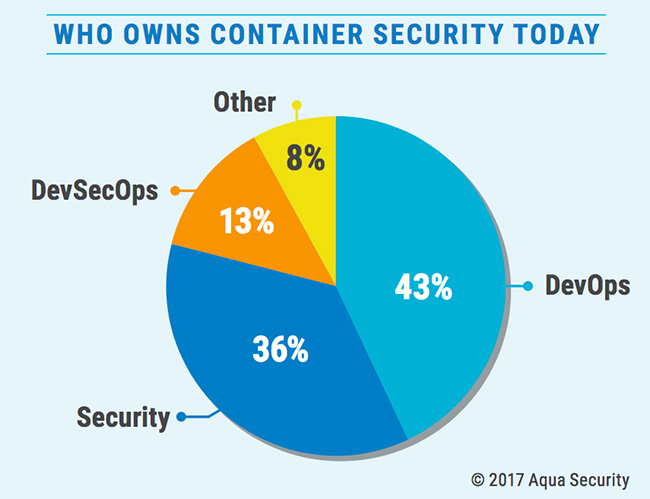
- Companies with multiple container applications in production place container security today in the hands of DevOps – future ownership is seen as shifting to DevSecOps.
“The impact can be felt not just in complex security architectures, but across any IT organization. Doctrinal change is a significant challenge, specifically empowering “end-to-end” involvement of DevOps teams across the security lifecycle. There should be clearly defined guiding principles that are baked into requirements and designs that prepare the DevSecOps teams to manage their new tasks,” Brian Alletto, senior architect in the security and infrastructure practice at West Monroe Partners, told Help Net Security.
“A careful assessment of roles and responsibilities in the new model must also be done to satisfy the new functional definitions while maintaining the same or better level of control and compliance across the application landscape. Additionally, use of DevOps automation toolsets in security operations can be a powerful force multiplier, but care must be taken to ensure their safe application to critical controls and processes,” Alletto concluded.
“The significant change that containers introduce to application delivery and deployment requires a more collaborative approach by security and DevOps teams. Organizations would do well to embed security early into the process, rather than apply security controls after the fact,” said Doug Cahill, Senior Analyst, Cybersecurity at Enterprise Strategy Group.