New infosec products of the week: March 2, 2018
Demisto brings visibility into SOC metrics
Demisto’s latest release of its Security Operations Platform enables customers to leverage the incident metrics through customizable dashboards and reports. CISOs can measure SOC health and business risk, SOC managers can measure analyst productivity and incident bottlenecks, and analysts can measure incident and indicator trends.

ESET Smart TV Security protects against rising malware threats
ESET Smart TV Security protects against targeted malware attacks on connected TVs and other devices on the Android TV operating system. The solution is available via Google Play, and can only be downloaded from a user’s TV device. Once installed, users will be protected by ESET across their entire Android ecosystem – both smartphone and TV.

User-centric network traffic analysis for insider threat detection and response
Corvil announced the new release of its Security Analytics solution, which helps organizations identify malicious behavior from compromised user accounts that increase the risk of data theft and reputational damage. By presenting a prioritized list of the most suspicious users in the environment as well as activity across associated devices of all types, security teams can see, understand and act on evasive threats and protect high-value assets.

get2Clouds: Send encrypted files, chat securely
NOS Microsystems released get2Clouds, an application that encrypts data and sends it where it needs to go. It features secure file transfers of unlimited size, secure cloud sync, an E2E encrypted messenger, separate corporate and private cloud profiles, and more. The solution is available as a mobile and desktop application.

Aricent launches intelligent security automation system
Aricent launched its Highly Automated Vulnerability Assessment Orchestration Containers (HAVOC) framework that manages cyber risk by catching security vulnerabilities before they are exploited. Aricent’s HAVOC solution addresses the need to understand the nature of vulnerability risk through a combination of precision coverage, superior probability and statistics, and speed of decision making.

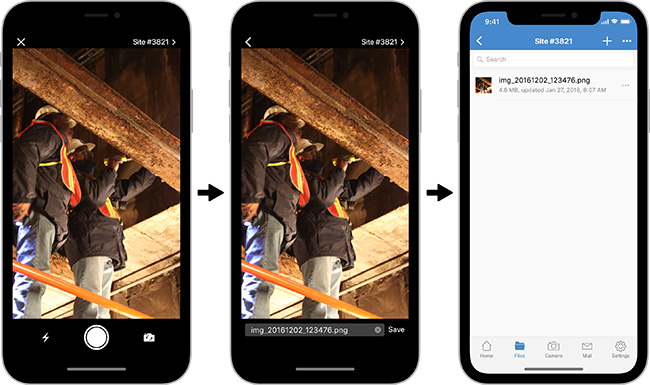
Access and share sensitive information on mobile devices
Board of director and executive presentations – these and other sensitive documents are the ones senior executives most often read and collaborate on. Accessing and sharing these documents from a smart phone or tablet therefore must be efficient while meeting security standards to maintain compliance with industry regulations, even when on the road. The security and compliance capabilities in the Accellion secure file sharing platform that enterprises rely so heavily on are also available in Accellion’s mobile app.