Microsoft Application Inspector: Check open source components for unwanted features
Want to know what’s in an open source software component before you use it? Microsoft Application Inspector will tell you what it does and spots potentially unwanted features – or backdoors.

About Microsoft Application Inspector
“At Microsoft, our software engineers use open source software to provide our customers high-quality software and services. Recognizing the inherent risks in trusting open source software, we created a source code analyzer called Microsoft Application Inspector to identify ‘interesting’ features and metadata, like the use of cryptography, connecting to a remote entity, and the platforms it runs on,” Guy Acosta and Michael Scovetta, security program managers at Customer Security and Trust, Microsoft, explained the Inspector’s genesis.
The Microsoft Application Inspector:
- Is a client .NET Core-based tool that can be run from a command line in Windows, Linux or MacOS
- Uses static analysis and a customizable JSON-based rules engine to analyze the target code. Users can add/edit/remove default rule patterns (there are over 500) as well as add their own rules
- Is able to analyze code written in a variety of programming languages
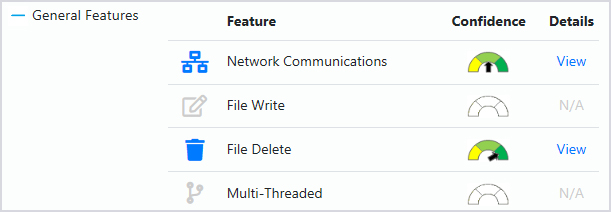
Once the tool does its work, it generates a HTML “report” that shows the features, project summary and meta-data detected (see image above). JSON and TEXT output format options are supported for those who prefer them.
Each discovered feature can be broken down into more specific categories and receives a confidence indicator. Users can see for themselves the source code snippets that produced each “discovery”.
Use cases
“Basically, we created Application Inspector to help us identify risky third party software components based on their specific features, but the tool is helpful in many non-security contexts as well,” the developers explained.
“For instance, it can also help identify feature deltas or changes between versions which can be critical for detecting injection of backdoors. Well constructed and hidden backdoors can go undetected by a tool that is only looking for poor security programming practices because it doesn’t look at context at a feature level.”
Nevertheless, the tool is not meant to replace security static analyzers or security code reviews, but to be used alongside them.
“Knowing what is in your software is the first step to making key choices about what actions are appropriate before allowing it to be deployed in your own or to customer environments. Our tool includes hundreds of default identifying patterns for detecting general features like frameworks used, file I/O, OS API’s as well as the ability to detect key security and privacy features of a component,” the developers concluded.
Microsoft Application Inspector is open source and available for download from GitHub.