Anomali XDR features extend visibility over a wider range of threat information sources
Anomali announced availability of its quarterly portfolio update. New XDR features and enhancements provide customers with the ability to align global threat intelligence with organizational security goals, extend visibility and integration over a wider range of threat information sources, detect threats with greater precision, and further optimize their response.
“Organizations facing talent shortages are burdened with resource-intensive false positives and non-stop cyberattacks. These conditions make it virtually impossible for disconnected teams that are dependent on siloed data to defend against modern adversaries,” said Mark Alba, Chief Product Officer, Anomali. “By bringing together the elements that make threat intelligence programs successful, we are providing our customers with capabilities that stop attackers and close breaches before they have a chance to disrupt normal business operations.”
With this release, Anomali customers receive a range of enhancements, and benefits:
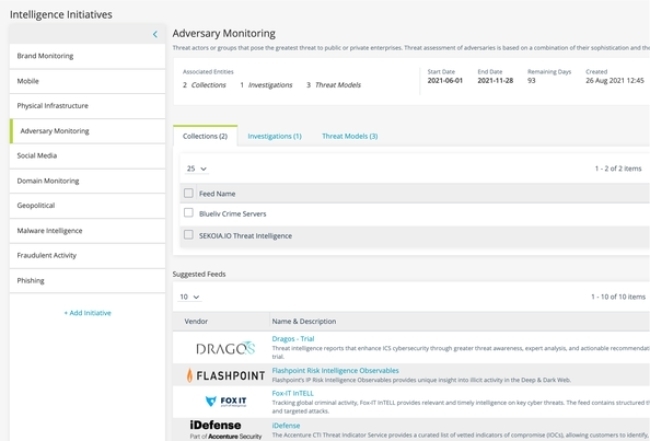
- Organizational goal alignment – The new Intelligence Initiatives feature breaks down information and operational silos, creating a foundation for security teams to collaborate cross-functionally, attribute analyst activity to investigations, and create relevant intelligence in support of organizational threat detection requirements.
- Expanded threat visibility and identification – Anomali Lens+ (an NLP-powered extension that scans web content to identify threats and operationalize intelligence) now comes with increased support for Microsoft Office 365, with an add-in to leverage Lens+ directly from Office 365 apps.
- Added strategic intelligence (beta) – Increased support for MITRE ATT&CK Sub-techniques in security controls and investigations makes it easier for security analysts to integrate threat intelligence into their investigations and threat detection processes. This release also provides the ability to switch between different versions of the MITRE ATT&CK framework, so that analysts can use the specific version needed for their investigations.
- Increased information sharing capabilities – As a leading innovator of threat information sharing between organizations and internal teams, we have added enhanced STIX 2.1 support for establishing object relationships. In this release, we’ve enabled users to create custom threat model objects as well as implemented support for STIX Relationship Objects (SROs) that represent types of relationships used to describe CTI.