7 open-source malware analysis tools you should try out
There are two main types of malware analysis: static and dynamic.
Performing static analysis of a malicious binary means concentrating on analyizing its code without executing it. This type of analysis may reveal to malware analysts not only what the malware does, but also its developer’s future intentions (e.g., currently unfinished functionalities).
Dynamic analysis looks at the behavior of the malware when it’s run – usually in a virtual sandbox. This type of analysis should reveal the malware’s behavor and any detection evasion techniques it uses.
Malware analysis benefits security analysts by allowing them to, among other things:
- Identify hidden indicators of compromise (IOCs).
- Boost the effectiveness of IOC notifications and warnings.
- Triage incidents according to severity.
All the malware analysis tools listed below can be freely downloaded and used.

capa: Automatically identify malware capabilities

capa detects capabilities in executable files. You run it against a PE, ELF, .NET module, or shellcode file and it tells you what it thinks the program can do. For example, it might suggest that the file is a backdoor, is capable of installing services, or relies on HTTP to communicate.

FLARE Obfuscated String Solver

The FLARE Obfuscated String Solver (FLOSS) uses advanced static analysis techniques to automatically deobfuscate strings from malware binaries. You can use it just like strings.exe to enhance basic static analysis of unknown binaries.

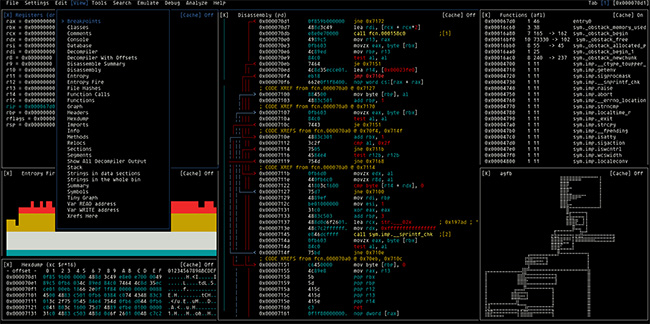
Ghidra Software Reverse Engineering Framework

Ghidra is a software reverse engineering (SRE) framework created and maintained by the National Security Agency Research Directorate. This framework includes a suite of full-featured, high-end software analysis tools that enable users to analyze compiled code on a variety of platforms including Windows, macOS, and Linux. Capabilities include disassembly, assembly, decompilation, graphing, and scripting, along with hundreds of other features.

Malcom: Malware Communication Analyzer

Malcom is a tool designed to analyze a system’s network communication using graphical representations of network traffic, and cross-reference them with known malware sources. This comes handy when analyzing how certain malware species try to communicate with the outside world.

Mobile Security Framework (MobSF)

MobSF is an automated, all-in-one mobile application (Android/iOS/Windows) pen-testing, malware analysis, and security assessment framework capable of performing static and dynamic analysis. MobSF supports mobile app binaries (APK, XAPK, IPA & APPX) along with zipped source code and provides REST APIs for seamless integration with your CI/CD or DevSecOps pipeline. The Dynamic Analyzer helps you to perform runtime security assessment and interactive instrumented testing.

Pafish: Testing tool

Pafish is a testing tool that uses different techniques to detect virtual machines and malware analysis environments in the same way that malware families do. The project is free and open source; the code of all the anti-analysis techniques is publicly available.

Radare2: The Libre Unix-like reverse engineering framework
The radare project started as a simple command-line hexadecimal editor focused on forensics. Today, Radare2 is a featureful low-level command-line tool with support for scripting. It can edit files on local hard drives, view kernel memory, and debug programs locally or via a remote gdb server. Radare2’s wide architecture support allows you to analyze, emulate, debug, modify, and disassemble any binary.

BONUS
theZoo: A live malware repository

theZoo is a repository of live malware. The project was created to offer a fast and easy way of retrieving malware samples and source code in an organized fashion in hopes of promoting malware research.
