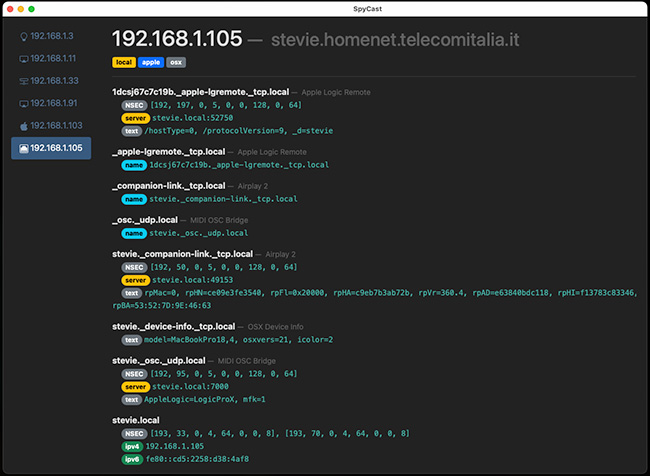
SpyCast: Cross-platform mDNS enumeration tool
SpyCast is a cross-platform mDNS enumeration tool that can work either in active mode by recursively querying services or in passive mode by only listening to multicast packets. You can download it on GitHub.
Simone Margaritelli, the tool’s author, answered a few questions for Help Net Security readers.
What was the motivation behind the creation of the tool?
I’m working on research that involves reverse engineering an Apple network protocol. Both the client and server sides of this protocol advertise their presence (with other essential information) on the network via mDNS. Other than discovering them, I also needed a quick way to check how this information changed over time. So, instead of using Wireshark and manually checking the packets, I coded SpyCast.
What challenges did you encounter during development?
mDNS is quite well documented and a relatively simple protocol. However, there aren’t many tools that organize the information in an easy-to-consume way. Most of them are terminal based and do not offer insights into what they are showing you.
What are your future plans for SpyCast?
The tool does everything I need already, but it would be nice adding the feature to impersonate a device on the network spoofing its mDNS responses. One use case for this could be impersonating a Chromecast device to receive the video stream of something DRM protected.