Anamarija Pogorelec

AI infrastructure is cracking under sovereignty demands
AI deployments are moving into environments with tighter controls around data, infrastructure, and system operations. Organizations are building AI systems across multiple …

Cybersecurity jobs available right now: May 19, 2026
CISO DataFence | Israel | Hybrid – No longer accepting applications As a CISO, you will develop security roadmaps, compliance plans, risk registers, policies, and …

201 arrested in INTERPOL disruption of phishing and fraud networks
Operation Ramz, a cybercrime initiative coordinated by INTERPOL across the MENA region, focused on disrupting phishing campaigns, malware activity, and cyber scams that caused …

AI shrinks vulnerability exploitation window to hours
Time has become organizations’ biggest vulnerability because the gap between vulnerability discovery and exploitation has narrowed to hours, according to Synack’s 2026 State …

Product showcase: McAfee + ChatGPT integration turns doubt into a scam check
McAfee + ChatGPT integration brings real-time scam detection in conversations and gives users an easier way to verify suspicious content before clicking or responding. It is …

When ransomware hits, confidence doesn’t restore endpoints
Ransomware, supply chain vulnerabilities, insider threats, compliance failures, and software disruptions remain major concerns for security leaders, according to The …

Debian 13.5 point release lands with security fixes, bug patches
Debian 13.5 is the fifth point release for the stable distribution “trixie.” The update folds in roughly 100 Debian Security Advisories and corrections for more …

The AI oversight paradox: Is the investment worth the cost of watching it?
Unlike in 2025, when AI adoption and testing drove business strategies, organizations in 2026 want proven ROI before committing budgets, according to a report by Globalization …

New infosec products of the week: May 15, 2026
Here’s a look at the most interesting products from the past week, featuring releases from Alation, Apricorn, Versa Networks, and TrustCloud. The questionnaire-based TPRM …
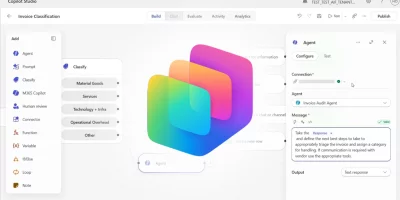
Microsoft turns Copilot Studio into an AI agent control center
The Microsoft Copilot Studio April 2026 updates improve visibility and governance for admins and expand workflow capabilities for managing agents. Copilot surfaces agent …

Over 70% of organizations hit by identity breaches
Attackers rely on stolen credentials, compromised service accounts, and social engineering attacks targeting employees, according to Sophos’ The State of Identity Security …

Machine identities outnumber humans 109 to 1
Organizations manage an average of 109 machine identities for every human identity. AI agents account for a growing share of those identities, with companies expecting AI …
Featured news
Resources
Don't miss
- $20 per zero-day is already the WordPress plugin reality
- Deleted Google API keys keep working for up to 23 minutes, researchers warn
- Meet Fractal, an OS made for microarchitecture reverse engineering
- Microsoft open-sources tools for designing and testing AI agents
- GitHub, Grafana Labs breaches traced back to TanStack supply chain compromise