Mirko Zorz

SecureClaw: Dual stack open-source security plugin and skill for OpenClaw
AI agent frameworks are being used to automate work that involves tools, files, and external services. That type of automation creates security questions around what an agent …

Your encrypted data is already being stolen
Quantum computing is often treated as a distant, theoretical cybersecurity issue. According to Ronit Ghose, Global Head, Future of Finance of Citi Institute, that mindset is …

REMnux v8 brings AI integration to the Linux malware analysis toolkit
REMnux, a specialized Linux distribution for malware analysis, has released version 8 with a rebuilt platform based on Ubuntu 24.04 and a new capability aimed at connecting AI …

Security at AI speed: The new CISO reality
The CISO role has changed significantly over the past decade, but according to John White, EMEA Field CISO, Torq, the most disruptive shift is accountability driven by agentic …

Edge computing’s biggest lie: “We’ll patch it later”
Edge computing is spreading fast, from factory floors to remote infrastructure. But many of these systems are hard to maintain once they are deployed. Devices may run old …

When security decisions come too late, and attackers know it
In this Help Net Security, Chris O’Ferrell, CEO at CodeHunter, talks about why malware keeps succeeding, where attackers insert malicious code in the SDLC, and how CI/CD …

OpenClaw Scanner: Open-source tool detects autonomous AI agents
A new free, open source tool is available to help organizations detect where autonomous AI agents are operating across corporate environments. The OpenClaw Scanner identifies …

Groupe Rocher CISO on strengthening a modern retail cybersecurity strategy
Global retail and beauty brands manage a unique cybersecurity balancing act. They depend on consumer trust, massive volumes of personal data, and a sprawling network of …

What happens when cybersecurity knowledge walks out the door
In this Help Net Security interview, Andrew Northern, Principal Security Researcher at Censys, explains why mentorship matters and what organizations risk losing when senior …

United Airlines CISO on building resilience when disruption is inevitable
Aviation runs on complex digital systems built for stability, safety, and long lifecycles. That reality creates a unique cybersecurity challenge for airlines, where disruption …
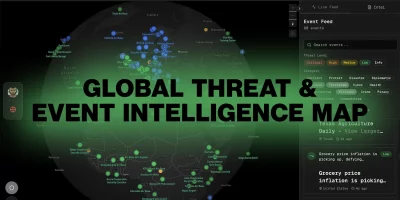
Global Threat Map: Open-source real-time situational awareness platform
Global Threat Map is an open-source project offering security teams a live view of reported cyber activity across the globe, pulling together open data feeds into a single …

When open science meets real-world cybersecurity
Scientific research environments are built for openness and collaboration, often prioritizing long-term discovery over traditional enterprise security. In this Help Net …
Featured news
Resources
Don't miss
- Download: Automating Pentest Delivery Guide
- Open-source privacy proxy masks PII before prompts reach external AI services
- cPanel zero-day exploited for months before patch release (CVE-2026-41940)
- Cisco releases open-source toolkit for verifying AI model lineage
- Nine-year-old Linux kernel flaw enables reliable local privilege escalation (CVE-2026-31431)