authentication

Field workers don’t need more access, they need better security
In this Help Net Security interview, Chris Thompson, CISO at West Shore Home, discusses least privilege and credential hygiene for a field-based workforce. He covers access …

Passwords, MFA, and why neither is enough
Passwords weren’t enough, so we added MFA. Now MFA isn’t enough either. In this Help Net Security video, Karlo Zatylny, CTO/CISO at Portnox, walks through why each …

Why workforce identity is still a vulnerability, and what to do about it
Most organizations believe they have workforce identity under control. New hires are verified. Accounts are provisioned. Multi-factor authentication is enforced. Audits are …

One stolen credential is all it takes to compromise everything
Attackers often gain access through routine workflows like email logins, browser sessions, and SaaS integrations. A single stolen credential can give them a quick path to move …

The defense industrial base is a prime target for cyber disruption
Cyber threats against the defense industrial base (DIB) are intensifying, with adversaries shifting from traditional espionage toward operations designed to disrupt production …

Design weaknesses in major password managers enable vault attacks, researchers say
Can cloud-based password managers that claim “zero-knowledge encryption” keep users’ passwords safe even if their encrypted-vault servers are compromised? …

Yubico previews passkey-enabled digital signatures in upcoming YubiKey 5.8 firmware
Yubico’s upcoming YubiKey 5.8 firmware introduces standardized APIs that integrate hardware-backed signatures with passkey authentication. To enable privacy-capable digital …
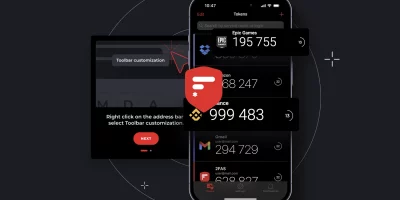
Product showcase: 2FAS Auth – Free, open-source 2FA for iOS
Online accounts usually rely on a password, but passwords alone can be weak if they’re reused, easily guessed, or stolen. Two-factor authentication (2FA) adds a second layer …

Microsoft sets a path to switch off NTLM across Windows
Windows is shifting to a more secure authentication approach, moving away from New Technology LAN Manager (NTLM) and toward stronger, Kerberos-based options. NTLM has been …

Microsoft Entra ID will auto-enable passkey profiles, synced passkeys
Starting March 2026, Microsoft Entra ID will automatically enable passkey profiles and introduce support for synced passkeys. Passkey profiles move into general availability …

The internet’s oldest trust mechanism is still one of its weakest links
Attackers continue to rely on domain names as an entry point into enterprise systems. A CSC domain security study finds that large organizations leave this part of their …

Wi-Fi evolution tightens focus on access control
Wi-Fi networks are taking on heavier workloads, more devices, and higher expectations from users who assume constant access everywhere. A new Wireless Broadband Alliance …
Featured news
Resources
Don't miss
- Critical Ivanti Sentry flaw allows root-level remote code execution (CVE-2026-10520)
- Record Microsoft Patch Tuesday, fresh zero-day
- Every set of AI guardrails can be broken by the right prompt
- The security in smartphones is helping send them to landfills
- Product showcase: Staying ahead of the threat horizon with Aunoo