authentication

Formal proofs expose long standing cracks in DNSSEC
DNSSEC is meant to stop attackers from tampering with DNS answers. It signs records so resolvers can verify that data is authentic and unchanged. Many security teams assume …

Session tokens give attackers a shortcut around MFA
In this Help Net Security video, Simon Wijckmans, CEO at cside, discusses why session token theft is rising and why security teams miss it. He walks through how web …

Passwordless is finally happening, and users barely notice
Security teams know the strain that comes from tightening authentication controls while keeping users productive. A new report from Okta suggests this strain is easing. …

Europe’s DMA raises new security worries for mobile ecosystems
Mobile security has long depended on tight control over how apps and services interact with a device. A new paper from the Center for Cybersecurity Policy and Law warns that …

New image signature can survive cropping, stop deepfakes from hijacking trust
Deepfake images can distort public debate, fuel harassment, or shift a news cycle before anyone checks the source. A new study from researchers at the University of Pisa …

What zero trust looks like when you build it step by step
In this Help Net Security video, Jonathan Edwards, Managing Director at KeyData Cyber, walks us through what practical zero trust adoption looks like in stages. He explains …

Social data puts user passwords at risk in unexpected ways
Many CISOs already assume that social media creates new openings for password guessing, but new research helps show what that risk looks like in practice. The findings reveal …

Why password management defines PCI DSS success
Most CISOs spend their days dealing with noisy dashboards and vendor pitches that all promise a shortcut to compliance. It can be overwhelming to sort out what matters. When …

The identity mess your customers feel before you do
Customer identity has become one of the most brittle parts of the enterprise security stack. Teams know authentication matters, but organizations keep using methods that …

Research shows identity document checks are missing key signals
Most CISOs spend their time thinking about account takeover and phishing, but identity document fraud is becoming a tougher challenge. A new systematic review shows how …

Is your password manager truly GDPR compliant?
Passwords sit at the core of every critical system, but many organizations still overlook how fragile their password workflows can be. When something goes wrong, security …
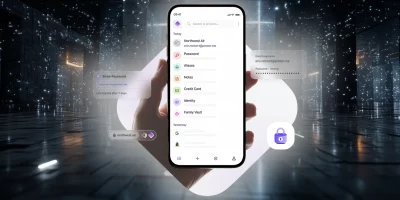
Product showcase: Proton Pass, a password manager with identity protection
Managing passwords can be a real headache, and it’s still common to fall back on reusing them or storing them in a browser without much protection. Proton Pass, built by the …
Featured news
Resources
Don't miss
- Cisco SD-WAN 0-day exploited, no patch available (CVE-2026-20245)
- June 2026 Patch Tuesday forecast: Where are the CVEs?
- AgentGG: Open-source agentic SAST scanner
- Thieves can pull off keyless car theft in under a minute and here’s how to stop them
- OAuth marketplace apps keep access after publishers vanish