automation

Most pros have seen AI hallucinations in IT operations
Autonomous AI is taking action inside enterprise IT environments. Software is restarting services, isolating risky devices, and applying patches without waiting for a human to …
Microsoft Scout agent opens a new category of always-on Autopilots
Workplace AI assistants have mostly waited for a prompt before doing anything. A user asks, the tool answers, and the exchange ends there. Microsoft is putting a different …

Microsoft’s new cloud PCs place AI agents under enterprise controls
Microsoft’s Windows 365 for Agents, a cloud PC platform for agentic workloads, runs AI agents in secure environments. Organizations can direct agents with natural language to …
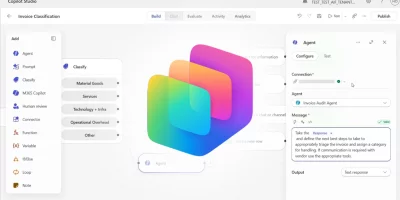
Microsoft turns Copilot Studio into an AI agent control center
The Microsoft Copilot Studio April 2026 updates improve visibility and governance for admins and expand workflow capabilities for managing agents. Copilot surfaces agent …

Security teams are turning to AI to survive alert overload
The World Economic Forum white paper “Empowering Defenders: AI for Cybersecurity” identified AI as the biggest driver of change in cybersecurity for 94% of survey respondents. …

Bad bots make up 40% of internet traffic
The normalization of AI and automation within internet infrastructure is changing how organizations interpret traffic. Activity that once appeared anomalous is now treated as …

OpenAI releases Symphony to automate Codex work through Linear
Engineering teams running coding agents at scale find themselves managing dozens of parallel sessions across browser tabs and command-line windows. OpenAI has released an …
Scenario: Open-source framework for automated AI app red-teaming
Enterprises running customer service bots, data analytics agents, and other AI-driven applications in production handle sensitive records and connect to core business systems …

PentAGI: Open-source autonomous AI penetration testing system
Penetration testers have long relied on collections of specialized tools, manual coordination, and documented runbooks to work through a target assessment. PentAGI, an …

OpenAI expands its cyber defense program with GPT-5.4-Cyber for vetted researchers
Defending critical software has long depended on the ability to find and fix vulnerabilities faster than attackers can exploit them. OpenAI is expanding a program designed to …

Anthropic’s new AI model finds and exploits zero-days across every major OS and browser
Automated vulnerability discovery tools have existed for decades, and the gap between finding a bug and building a working exploit has always slowed attackers. That gap is now …

AI SOC vendors are selling a future that production deployments haven’t reached yet
Vendors selling AI-powered security operations platforms have built their pitches around a consistent set of promises: autonomous threat investigation, dramatic reductions in …
Featured news
Resources
Don't miss
- LiteLLM vulnerability under active attack, CISA warns (CVE-2026-42271)
- The architecture of subtraction: Why it’s time to erase the roads, not just map the traffic
- Treating AI agents like service accounts for federated query security
- Malware ships with bugs that defenders could use against it
- Qilin ransomware affiliate exploited Check Point VPN zero-day (CVE-2026-50751)