cybersecurity

OpenAI joins the race in AI-assisted code security
OpenAI introduced Codex Security, an AI agent that reviews codebases to find, verify, and help fix software vulnerabilities. The launch comes a few weeks after rival …

Decoding silence: How deaf and hard-of-hearing pros are breaking into cybersecurity
Stu Hirst was already a CISO when he started to go deaf. It was 2023, and the hearing loss crept in over months, enough for him to adapt, to lean on hearing aids and captions, …

Open-source tool Sage puts a security layer between AI agents and the OS
Autonomous AI agents running on developer workstations execute shell commands, fetch URLs, and write files with little or no inspection of what they are doing. Open-source …
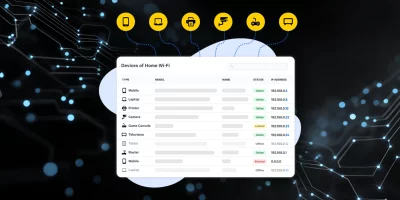
Product showcase: Fing Desktop puts network visibility on your screen
Phones, laptops, smart TVs, cameras, and smart home equipment all use the same network. Knowing what’s connected helps users manage performance and security. Fing Desktop …

Microsoft working on Teams feature to keep unauthorized bots at bay
Microsoft plans to add a new Teams feature that lets meeting admins identify and control third-party bots before they join. According to the Microsoft 365 Roadmap, the feature …

New cyber module strengthens risk planning for health organizations
The Administration for Strategic Preparedness and Response’s (ASPR) new cybersecurity module in the Risk Identification and Site Criticality (RISC) 2.0 Toolkit helps …

OpenAI’s GPT-5.4 doubles down on safety as competition heats up
In the midst of recent developments and controversies surrounding a contract with the U.S. Department of Defense, OpenAI released the GPT-5.4 model. The release comes at a …

March 2026 Patch Tuesday forecast: Is AI security an oxymoron?
Developers and analysts are using more AI tools to produce code and to test both the performance and security of the finished products. They are also embedding AI …

Backup strategies are working, and ransomware gangs are responding with data theft
Business email compromise (BEC) and funds transfer fraud combined for 58% of all cyber insurance claims filed in 2025, according to data from Coalition covering more than …

Why phishing still works today
In this Help Net Security video, Gal Livschitz, Senior Penetration Tester at Terra Security, explains how phishing has evolved and why employees still fall for it. He outlines …

Western governments lay the groundwork for secure 6G networks
Governments are preparing for 6G, the next generation of mobile networks, placing security and resilience among their top priorities. In response, seven countries …

What happens when AI teams compete against human hackers
A cybersecurity competition produced what may be the largest controlled dataset comparing AI-augmented teams to human-only teams on professional-grade offensive security …
Featured news
Resources
Don't miss
- Hackers hijacked CPUID downloads, served STX RAT to victims
- Adobe issues emergency fix for Acrobat Reader flaw exploited in the wild (CVE-2026-34621)
- Fixing vulnerability data quality requires fixing the architecture first
- ZeroID: Open-source identity platform for autonomous AI agents
- MITRE releases a shared fraud-cyber framework built from real attack data