
LockBit 5.0 ransomware expands its reach across Windows, Linux, and ESXi
The Acronis Threat Research Unit (TRU) has identified a new and significantly enhanced version of the LockBit ransomware, LockBit 5.0, currently being deployed in active …

Trojanized 7-Zip downloads turn home computers into proxy nodes
A trojanized version of the popular 7-Zip software is quietly turning home computers into residential proxy nodes, Malwarebytes warns. Spurred by a Reddit post in which a user …

Poland’s energy control systems were breached through exposed VPN access
On 29 December 2025, coordinated cyberattacks unfolded across Poland’s critical infrastructure, targeting energy and industrial organizations. The attackers struck numerous …

eScan AV users targeted with malicious updates
The update infrastructure for eScan antivirus, a product of Indian cybersecurity company MicroWorld Technologies, has been compromised by unknown attackers to deliver a …

Open-source malware zeroes in on developer environments
Open source malware activity during 2025 concentrated on a single objective: executing code inside developer environments, according to Sonatype. The focus reflected a broader …

A fake romance turns into an Android spyware infection
ESET researchers have identified an Android spyware campaign that uses romance scam tactics to target individuals in Pakistan. The operation relies on a malicious app …

WinRAR vulnerability still a go-to tool for hackers, Mandiant warns
State-sponsored hackers and financially motivated attackers continue leveraging a critical WinRAR vulnerability (CVE-2025-8088) that’s been fixed over half a year ago. …

Attackers use Windows App-V scripts to slip infostealer past enterprise defenses
A malware delivery campaign detailed by Blackpoint researchers employs an impressive array of tricks to deliver an infostealer to employees without triggering enterprise …

Poland repels data-wiping malware attack on energy systems
Suspected Russian cyber attackers tried to take down parts of Poland’s energy infrastructure with new data-wiping malware – and failed. According to information shared …

Linux users targeted by crypto thieves via hijacked apps on Snap Store
Cryptocurrency thieves have found a new way to turn trusted software packages for Linux on the Snap Store into crypto-stealing malware, Ubuntu contributor and former Canonical …
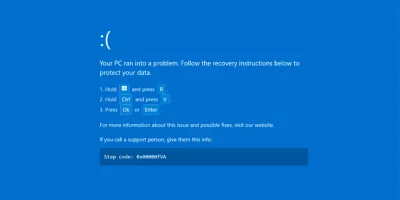
Fake Booking.com emails and BSODs used to infect hospitality staff
Suspected Russian attackers are targeting the hospitality sector with fake Booking.com emails and a fake “Blue Screen of Death” to deliver the DCRat malware. The …

Budding infosec pros and aspiring cyber crooks targeted with fake PoC exploits
Malware peddlers are targeting infosec enthusiasts, budding security professionals, and aspiring hackers with the Webrat malware, masquerading the threat as proof-of-concept …
Featured news
Resources
Don't miss
- LiteLLM vulnerability under active attack, CISA warns (CVE-2026-42271)
- The architecture of subtraction: Why it’s time to erase the roads, not just map the traffic
- Treating AI agents like service accounts for federated query security
- Malware ships with bugs that defenders could use against it
- Qilin ransomware affiliate exploited Check Point VPN zero-day (CVE-2026-50751)