
OpenAI tackles a bad habit people have when interacting with AI
Since people tend to paste personal data into AI tools such as ChatGPT, OpenAI has released Privacy Filter, an open-weight model designed to detect and redact personally …

A year in, Zoom’s CISO reflects on balancing security and business
In this Help Net Security interview, Sandra McLeod, CISO at Zoom, reflects on her first year in the role. She talks about moving from reactive firefighting to business …
Scenario: Open-source framework for automated AI app red-teaming
Enterprises running customer service bots, data analytics agents, and other AI-driven applications in production handle sensitive records and connect to core business systems …

GDPR works, but only where someone enforces it
A new measurement study of web tracking across ten countries offers a reality check for anyone working on privacy compliance. Researchers crawled the same set of globally …
Ransomware, fraud, and lawsuits drive cyber insurance claims to new peaks
The 2026 InsurSec Report from At-Bay, covering more than 100,000 policy years of claims data, documents a 7% year-over-year rise in overall claim frequency and an all-time …
Google’s Workspace Intelligence promises privacy while running on your data
Security and data governance are among the key considerations in Google’s latest AI update, which introduces Workspace Intelligence within Google Workspace. Google describes …

Cyberattack on French government agency triggers phishing alert
France Titres, a French government agency, has disclosed a data breach that may have exposed user data from its online portal. France Titres, also known as the Agence …

Claude Mythos finds 271 Firefox flaws, Mozilla believes it shifts security toward defenders
The Mozilla Foundation tested Claude Mythos, an Anthropic AI model that has stirred debate in the cybersecurity community. Before granting access to Mythos, Mozilla scanned …

New Mirai variants target routers and DVRs in parallel campaigns
Hidden inside newly discovered botnet malware is an unusual message from its creator: “AI.NEEDS.TO.DIE”. Dubbed “tuxnokill” by researchers at Akamai, …

Progress Software fixes sneaky WAF bypass vulnerability (CVE-2026-21876)
Progress Software has fixed a slew of high-severity vulnerabilities in MOVEit WAF and LoadMaster, including a flaw (CVE-2026-21876) that may allow attackers to bypass firewall …
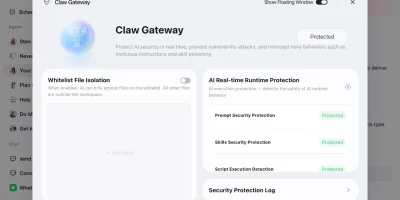
Tencent’s QClaw AI agent app arrives on Windows and macOS
Tencent has opened an international beta of QClaw, an AI agent application aimed at consumers in Canada, Japan, Singapore, South Korea, and the United States. The first wave …

Phishing reclaims the top initial access spot, attackers experiment with AI tools
Phishing returned as the leading method attackers used to break into organizations in the first quarter of 2026, accounting for over a third of engagements where initial …
Featured news
Resources
Don't miss
- Lessons for organizations from the Verizon 2026 Data Breach Investigations Report
- OpenHack: Open-source AI-powered vulnerability research
- Boards want cyber risk in dollars, not CVE counts
- $20 per zero-day is already the WordPress plugin reality
- Deleted Google API keys keep working for up to 23 minutes, researchers warn