Product showcase: TrackerControl lets Android users see who’s tracking them
TrackerControl is an open-source Android application designed to give users visibility into and control over the hidden data within mobile apps. Many apps routinely …
Security teams are paying more attention to the energy cost of detection
Security teams spend a lot of time explaining why detection systems need more compute. Cloud bills rise, models retrain more often, and new analytics pipelines get added to …

Wi-Fi evolution tightens focus on access control
Wi-Fi networks are taking on heavier workloads, more devices, and higher expectations from users who assume constant access everywhere. A new Wireless Broadband Alliance …
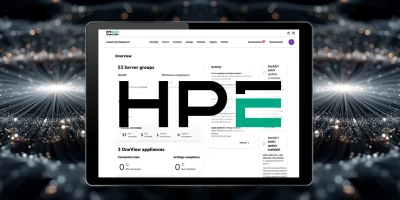
Recently fixed HPE OneView flaw is being exploited (CVE-2025-37164)
An unauthenticated remote code execution vulnerability (CVE-2025-37164) affecting certain versions of HPE OneView is being leveraged by attackers, CISA confirmed by adding the …

PoC released for unauthenticated RCE in Trend Micro Apex Central (CVE-2025-69258)
Trend Micro has released a critical patch fixing several remotely exploitable vulnerabilities in Apex Central (on-premise), including a flaw (CVE-2025-69258) that may allow …

IPFire update brings new network and security features to firewall deployments
Security and operations teams often work with firewall platforms that require frequent tuning or upgrades to meet evolving network demands. IPFire has released its 2.29 Core …

Cybercriminals are scaling phishing attacks with ready-made kits
Phishing-as-a-Service (PhaaS) kits lower the barrier to entry, enabling less-skilled attackers to run large-scale, targeted phishing campaigns that impersonate legitimate …

StackRox: Open-source Kubernetes security platform
Security teams spend a lot of time stitching together checks across container images, running workloads, and deployment pipelines. The work often happens under time pressure, …

What happens to insider risk when AI becomes a coworker
In this Help Net Security video, Ashley Rose, CEO at Living Security, discusses how AI is changing insider risk. AI is now built into daily work across departments, which …

Passwords are where PCI DSS compliance often breaks down
Most PCI DSS failures do not start with malware or a targeted attack. They start with everyday behavior. Reused passwords. Credentials stored in spreadsheets. Shared logins …

Voice cloning defenses are easier to undo than expected
Many voice protection tools promise to block cloning by adding hidden noise to speech. Researchers at a Texas university found that widely used voice protection methods can be …

UK announces grand plan to secure online public services
The UK has announced a new Government Cyber Action Plan aimed at making online public services more secure and resilient, and has allocated £210 million (approximately $283 …
Featured news
Resources
Don't miss
- State-backed phishing attacks targeting military officials and journalists on Signal
- Poland’s energy control systems were breached through exposed VPN access
- CISA orders US federal agencies to replace unsupported edge devices
- Ransomware attackers are exploiting critical SmarterMail vulnerability (CVE-2026-24423)
- February 2026 Patch Tuesday forecast: Lots of OOB love this month