
Ransomware keeps widening its reach
Ransomware keeps shifting into new territory, pulling in victims from sectors and regions that once saw fewer attacks. The latest Global Threat Briefing for H2 2025 from …

Uneven regulatory demands expose gaps in mobile security
Mobile networks carry a great deal of the world’s digital activity, which makes operators a frequent target for attacks. A study released by the GSMA shows that operators …

New infosec products of the week: December 12, 2025
Here’s a look at the most interesting products from the past week, featuring releases from Apptega, Backslash Security, BigID, Black Kite, Bugcrowd, NinjaOne, Nudge Security, …

40 open-source tools redefining how security teams secure the stack
Open source security software has become a key way for teams to get flexibility, transparency, and capability without licensing costs. The free tools in this roundup address …

LLM vulnerability patching skills remain limited
Security teams are wondering whether LLMs can help speed up patching. A new study tests that idea and shows where the tools hold up and where they fall short. The researchers …

Password habits are changing, and the data shows how far we’ve come
In this Help Net Security video, Andréanne Bergeron, Security Researcher at Flare, explains how changes in user habits, policy shifts, and new tools have shaped password …
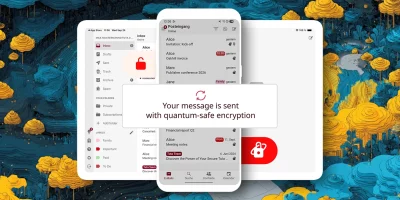
Product showcase: Tuta – secure, encrypted, private email
Tuta, formerly known as Tutanota, is built for anyone who wants email that stays private. Instead of treating encryption like a bonus feature, the service encrypts almost …

Teamwork is failing in slow motion and security feels it
Security leaders often track threats in code, networks, and policies. But a quieter risk is taking shape in the everyday work of teams. Collaboration is getting harder even as …

Henkel CISO on the messy truth of monitoring factories built across decades
In this Help Net Security interview, Stefan Braun, CISO at Henkel, discusses how smart manufacturing environments introduce new cybersecurity risks. He explains where single …

The hidden dynamics shaping who produces influential cybersecurity research
Cybersecurity leaders spend much of their time watching how threats and tools change. A new study asks a different question, how has the research community itself changed over …

UTMStack: Open-source unified threat management platform
UTMStack is an open-source unified threat management platform that brings SIEM and XDR features into one system. The project focuses on real time correlation of log data, …

LLMs are everywhere in your stack and every layer brings new risk
LLMs are moving deeper into enterprise products and workflows, and that shift is creating new pressure on security leaders. A new guide from DryRun Security outlines how these …
Featured news
Resources
Don't miss
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)
- Acrobat Reader zero-day exploited in the wild for many months
- AI agent intent is a starting point, not a security strategy
- Asqav: Open-source SDK for AI agent governance
- BlueHammer: Windows zero-day exploit leaked