Researchers discover highly stealthy Microsoft Exchange backdoor
An extremely stealthy Microsoft Exchange backdoor can read, modify or block emails going through the compromised mail server and even compose and send new emails.

LightNeuron – as the backdoor has been dubbed by ESET researchers – is remotely controlled via emails using steganographic PDF and JPG attachments and is believed to have been used by the Turla cyber espionage group.
About LightNeuron
The LightNeuron backdoor is the first known instance of a backdoor employing a malicious Microsoft Exchange Transport Agent as a persistence mechanism.
“Microsoft Exchange allows extending its functionalities using Transport Agents that can process and modify all email messages going through the mail server. Transport Agents can be created by Microsoft, third-party vendors, or directly within an organization,” the researchers explained.
“The typical events handled by a Transport Agent occur when the mail server sends or receives an email. Before the event is actually executed, the Transport Agents are called and have the possibility to modify or block the email.”
They are usually used for legitimate purposes, but as we can see in this instance they can also be used for malicious ones.
Aside from the Transport Agent, which is dropped in the Exchange folder located in the Program Files folder and registered in the mail server’s configuration, the backdoor also uses a DLL file containing most of the malicious functions needed by the Transport Agent.
As mentioned before, the backdoor can block emails, modify their body, recipient and subject, created a new email, replace attachments, and re-create and re-send the email from the Exchange server to bypass the spam filter.
It can create email and attachment logs, encrypt emails and store then, and parse JPG/PDF attachments and decrypt and execute the commands found in them.
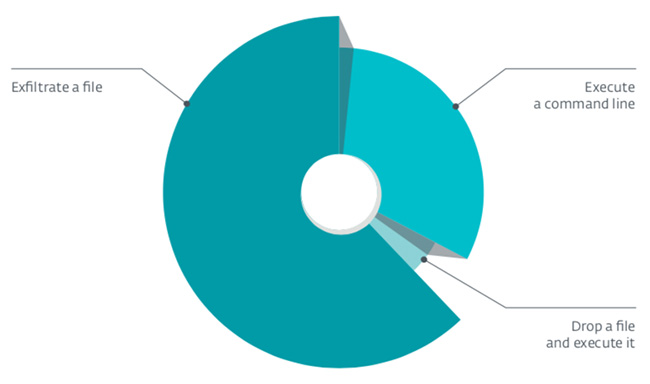
LightNeuron can also be instructed to write and execute files, delete and exfiltrate them, execute processes, disable itself, perform extensive logging (backdoor actions, debug, error, etc.) and perform automatic file exfiltration at a particular time of the day and night.
During their investigation, the researchers also noticed alongside LightNeuron the presence of tools like Remote Administration Software, RPC- based malware or .NET web shells targeting Outlook Web Access. By leveraging them, the attackers are able to control other machines on the local network using emails sent to the Exchange server.
Finally, judging by some strings decrypted from the malware samples, they believe its likely that a Linux variant of the malware exists and is used.
“That would not be surprising, given that many organizations have Linux mail servers,” they noted.
About Turla
Turla (aka Snake, aka Uroburos) is believed to be a Russian-speaking group of attackers that is likely state-sponsored. They’ve been active for more than a decade.
Their usual targets are government entities, diplomatic entities, military organizations and defense contractors, regional political organizations and research and education organizations around the world.
Even though LightNeuron dates back to at least 2014, it was discovered and analyzed by security researchers only now because of the previously unseen persistence mechanism, because it is hard to detect at the network level (no standard HTTP(S) communications), and because Turla deploys it only against its most important targets.
“This malware is not highly prevalent in the wild so it was able to stay under the radar for a long period of time,” ESET malware researcher Matthieu Faou told Help Net Security.
“We found LightNeuron while investigating machines already infected with known Turla malware. That’s how we were able to make the link between LightNeuron and Turla.”
The researchers pinpointed two targets hit with the backdoor: a Ministry of Foreign affairs in an Eastern European country and a regional diplomatic organization in the Middle East.
Removing the malware
ESET researchers have released IoCs for companies to check whether they’ve been with the malware, but warned against removing the two malicious files as the first order of business, as this will break Microsoft Exchange and prevent everybody in the organization from sending and receiving emails.
Administrators must first disable the malicious Transport Agents and then move to remove the two malicious files.
“If you do not plan to re-install the mail server, an important last step is to modify the passwords of all accounts that have administrative rights on the compromised server. Otherwise, attackers could access the server again to compromise it again,” they advised.