RansomHouse: Bug bounty hunters gone rogue?
A new cybercrime outfit that calls itself RansomHouse is attempting to carve out a niche of the cyber extortion market for itself by hitting organizations, stealing their data, and offering to delete it and provide a full report on how and what vulnerabilities were exploited in the process – all for a fee, of course.
“The thing is that, at least according to what they claim, RansomHouse’s sole purpose is not to act as another ransomware group, but rather to act as a pentesting/bug bounty group that forces their services on whoever does not take organizational security seriously enough,” Cyberint researchers told Help Net Security.
“We haven’t seen a report being sent to any victim, but we assume that at the stage they currently are, they try to build the reputation of a reliable group and will deliver the reports once the negotiation is successful.”
RansomHouse’s unusual approach to data extortion
How the group breaches the target companies is not known at this time, but they profess they do not to encrypt organizations’ data, just steal it and promise to delete it if they get paid. If they victim doesn’t pay up, they either attempt to sell the stolen data or, if no one is interested in buying, to leak it online for everyone to see.
“The no-encryption approach is a technique we have seen on the rise lately, although its effect is not always what the threat groups might hope for,” the researchers told Help Net Security.
“Overall, this technique will not work on any organization, and it depends on what type of data was stolen. For example, this technique will have a much higher success rate on organizations that working on secret projects or patents rather than a company whose leak contains a minor number of customers’ information. Profiling is something many threat groups (ransomware or data breach) do very often before targeting a victim to see what amounts to ask for, and what extorsion technique should be applied.”
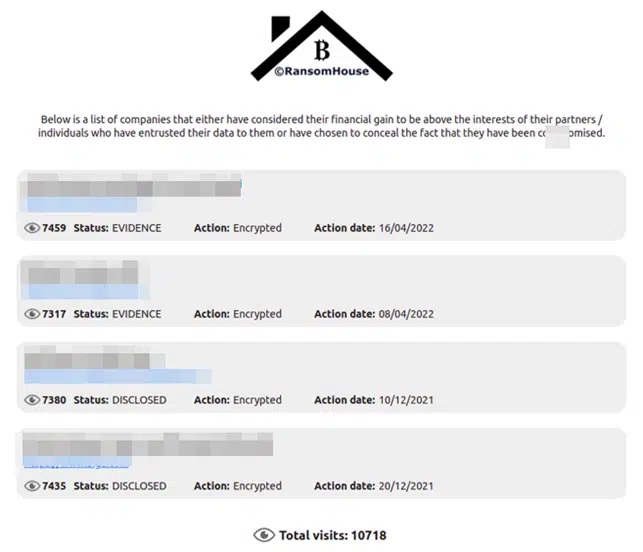
For the moment, the group’s website lists four organizations that have refused to pay the ransom. Though RansomHouse claims not to encrypt targets’ data, on their “naming and shaming” site they explicitly say that they used encrypted the data of each of the victims.
The researchers believe the discrepancy might be down to the group being still in “the stage where they are adopting their threat group’s identity, thus trying few techniques each victim.”
Is the group successful?
By analyzing the contents of the group’s Telegram channels, the researchers believe the group might have a blue and red team background and might even be disgruntled bug bounty hunters.
While definitely interested in the money, “they try to make it as painless as possible for their victims and conduct themselves in a straightforward manner.”
It’s difficult to tell how successful RansomHouse is, though.
Every compromised organization weighs the pros and cons of paying the ransom. After all, there is no guarantee that the stolen data will be deleted and not resold or leaked.
Additionally, some might count on the fact that recent research has shown that minor data breaches that received little negative media attention can end up having a positive effect, “as more people learn about the company and its products and dismiss the breach as bad luck.”