5 free resources from the Cybersecurity and Infrastructure Security Agency (CISA)
The Cybersecurity and Infrastructure Security Agency (CISA) is an agency of the United States Department of Homeland Security. CISA is in charge of enhancing cybersecurity and infrastructure protection at all levels of government, coordinating cybersecurity initiatives with American U.S. states, and enhancing defenses against cyberattacks.
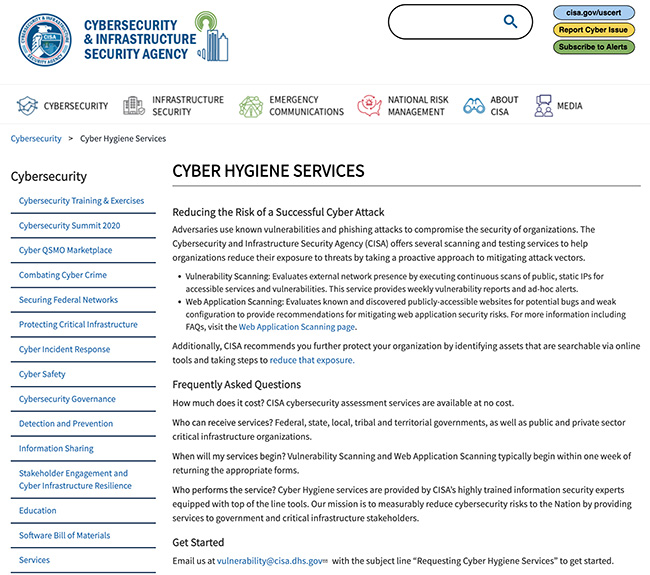
To assist businesses in enhancing their security capabilities, CISA offers free cybersecurity products and services.

Cyber Hygiene Vulnerability Scanning
You can register for this service by emailing vulnerability@cisa.dhs.gov. Scanning will start within 3 days, and you’ll begin receiving reports within two weeks. Once initiated, this service is mostly automated and requires little direct interaction.

Cybersecurity Evaluation Tool (CSET)
This tool provides organizations with a structured and repeatable approach to assessing the security posture of their cyber systems and networks. It includes both high-level and detailed questions related to all industrial control and IT systems.


Checklist for implementing cybersecurity measures
This document outlines four goals for your organization:
- Reducing the likelihood of a damaging cyber incident
- Detecting malicious activity quickly
- Responding effectively to confirmed incidents
- Maximizing resilience.


Known Exploited Vulnerabilities (KEV) Catalog
The KEV Catalog enables you to identify known software security flaws. You can search for software used by your organization and, if it’s found, update it to the most recent version in accordance with the vendor’s instructions.


Malcolm network traffic analysis tool suite
Malcolm is comprised of several widely used open source tools, making it an attractive alternative to security solutions requiring paid licenses.
The tool accepts network traffic data in the form of full packet capture (PCAP) files and Zeek logs. Visibility into network communications is provided through two interfaces: OpenSearch Dashboards, a data visualization plugin with dozens of prebuilt dashboards providing an at-a-glance overview of network protocols; and Arkime, a tool for finding and identifying the network sessions comprising suspected security incidents. All communications with Malcolm, both from the user interface and from remote log forwarders, are secured with industry standard encryption protocols.
Malcolm operates as a cluster of Docker containers, isolated sandboxes which each serve a dedicated function of the system.

