Anamarija Pogorelec

Gmail’s end-to-end encryption comes to mobile, no extra apps required
Google has expanded Gmail client-side encryption to Android and iOS devices, allowing users to engage with their organization’s most sensitive data on mobile devices while …

Product showcase: Session, a messenger without phone numbers or metadata
Instant messaging has been around for decades, but it became widely adopted with the emergence of smartphones. Earlier, communication was limited to basic text messages. …

New infosec products of the week: April 10, 2026
Here’s a look at the most interesting products from the past week, featuring releases from Advenica, Intruder, Mallory, and Secureframe. Mallory brings contextual threat …
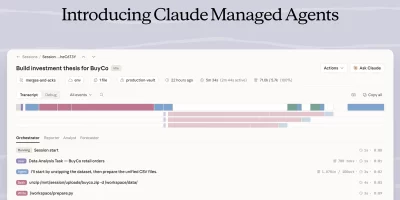
Claude Managed Agents bring execution and control to AI agent workflows
Anthropic’s Claude Managed Agents are a suite of composable APIs for building and deploying cloud-hosted agents at scale, handling sandboxed code execution, …

Meta’s Muse Spark takes AI a step closer to personal superintelligence
Meta Superintelligence Labs has introduced Muse Spark, a natively multimodal reasoning model with support for tool use, visual chain of thought, and multi-agent orchestration. …

Iranian cyber activity hits US energy, water, and government networks
U.S. government agencies on Tuesday warned American organizations about ongoing cyber activity targeting OT and PLC devices, including those manufactured by Rockwell …

Flatpak 1.16.4 fixes sandbox escape and three other security flaws
Flatpak, a Linux application sandboxing and distribution framework, released version 1.16.4, patching four security vulnerabilities. The most severe fix addresses a complete …

Anthropic’s new AI model finds and exploits zero-days across every major OS and browser
Automated vulnerability discovery tools have existed for decades, and the gap between finding a bug and building a working exploit has always slowed attackers. That gap is now …

Cybersecurity jobs available right now: April 8, 2026
Application Security Engineer Liebherr Group | Germany | On-site – View job details As an Application Security Engineer, you will implement security testing tools such …

AI-enabled device code phishing campaign exploits OAuth flow for account takeover
A phishing campaign that bypasses the standard 15-minute expiration window through automation and dynamic code generation, leveraging the OAuth Device Code Authentication flow …

GitHub Copilot CLI gets a second-opinion feature built on cross-model review
Coding agents make decisions in sequence: a plan is drafted, implemented, then tested. Any error introduced early compounds as subsequent steps build on the same flawed …

Comp AI: The open-source way to get compliant with SOC 2, ISO 27001, HIPAA and GDPR
Getting a startup through a SOC 2 audit has long meant months of manual evidence collection, policy writing, and repeated back-and-forth with auditors. A growing number of …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)