Anamarija Pogorelec

Cybersecurity jobs available right now: January 13, 2026
CISO CSIRO | Australia | Remote – No longer accepting applications As a CISO, you will lead and manage CSIRO’s cyber security strategy and program in alignment with the …

Claude connects to more healthcare data under security oversight
Healthcare teams are evaluating a range of AI tools for workflows tied to coverage, coding, care coordination, and trials. Anthropic announced expanded healthcare and life …

Debian 13.3 is now available with targeted corrections, updates
Debian 13.3 is the third maintenance update for the stable Debian 13 distribution, codenamed “trixie”. It updates package content to address security and other issues reported …

Downtime pushes resilience planning into security operations
CISOs describe a shift in how they define success. New research from Absolute Security shows broad agreement that resilience outweighs security goals centered on prevention …
Product showcase: TrackerControl lets Android users see who’s tracking them
TrackerControl is an open-source Android application designed to give users visibility into and control over the hidden data within mobile apps. Many apps routinely …
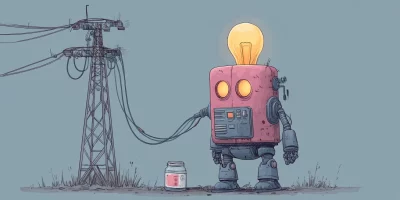
Security teams are paying more attention to the energy cost of detection
Security teams spend a lot of time explaining why detection systems need more compute. Cloud bills rise, models retrain more often, and new analytics pipelines get added to …

Wi-Fi evolution tightens focus on access control
Wi-Fi networks are taking on heavier workloads, more devices, and higher expectations from users who assume constant access everywhere. A new Wireless Broadband Alliance …

IPFire update brings new network and security features to firewall deployments
Security and operations teams often work with firewall platforms that require frequent tuning or upgrades to meet evolving network demands. IPFire has released its 2.29 Core …

Cybercriminals are scaling phishing attacks with ready-made kits
Phishing-as-a-Service (PhaaS) kits lower the barrier to entry, enabling less-skilled attackers to run large-scale, targeted phishing campaigns that impersonate legitimate …

StackRox: Open-source Kubernetes security platform
Security teams spend a lot of time stitching together checks across container images, running workloads, and deployment pipelines. The work often happens under time pressure, …

Debian seeks volunteers to rebuild its data protection team
The Debian Project is asking for volunteers to step in after its Data Protection Team became inactive. All three members of the team stepped down at the same time, leaving no …

What European security teams are struggling to operationalize
European security and compliance teams spend a lot of time talking about regulation. A new forecast report from Kiteworks suggests the harder problem sits elsewhere. According …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)