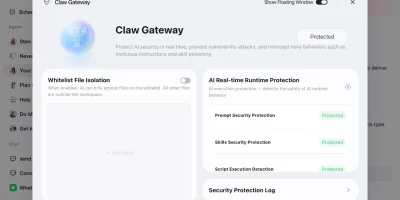
Tencent’s QClaw AI agent app arrives on Windows and macOS
Tencent has opened an international beta of QClaw, an AI agent application aimed at consumers in Canada, Japan, Singapore, South Korea, and the United States. The first wave …

PentAGI: Open-source autonomous AI penetration testing system
Penetration testers have long relied on collections of specialized tools, manual coordination, and documented runbooks to work through a target assessment. PentAGI, an …

Apple Intelligence flaw kept stolen tokens reusable on another device
Apple claims that Apple Intelligence, a GenAI service provided on its operating systems, is designed with an extra focus on user security and privacy through a two-stage …

OpenAI’s Chronicle feature lets Codex read your screen, raising privacy concerns
OpenAI’s Chronicle is a feature designed to help Codex, an AI-powered coding assistant, better understand what users are working on by capturing context directly from their …

Researchers build an encrypted routing layer for private AI inference
Organizations in healthcare, finance, and other sensitive industries want to use large AI models without exposing private data to the cloud servers running those models. A …

AI platform ATHR makes voice phishing a one-person job
For $4,000 and a cut of the take, a lone criminal can now run a fully automated voice-phishing operation via ATHR, a plaform that spoofs emails alerts from Google, Microsoft, …

Google wipes out 602 million scam ads with Gemini on duty
Google claims that its security teams work around the clock using its Gemini AI models to detect and stop harmful ads. “Bad actors are using generative AI to create …

Mozilla challenges enterprise AI providers with Thunderbolt, open-source AI client under your control
For organizations that want to keep company data within their own systems and have more control over how AI is deployed, Mozilla is offering an alternative to externally …

Codex can now operate between apps. Where are the boundaries?
OpenAI is rolling out a major update to the Codex desktop app for users signed in with ChatGPT. Personalization features, including context-aware suggestions and memory, will …

Anthropic releases Claude Opus 4.7 with automated cybersecurity safeguards
Software teams building agentic AI workflows have been pushing frontier models toward longer, unsupervised task runs. Claude Opus 4.7, now generally available from Anthropic, …

OpenAI updates Agents SDK, adds sandbox for safer code execution
OpenAI’s updated Agents SDK helps developers build agents that inspect files, run commands, edit code, and handle tasks within controlled sandbox environments. The update …
Command integrity breaks in the LLM routing layer
Systems that rely on LLM agents often send requests through intermediary routing services before reaching a model. These routers connect to different providers through a …
Featured news
Resources
Don't miss
- LinkedIn-themed phishing abuses Adobe’s A/B testing platform
- The behavioral signals that sharpen Trojan malware detection
- Zapier exploit chain shows how known anti-patterns compose into critical risk
- The CISO selling confidence in a market full of breach headlines
- Frontier AI models collapse under multi-turn AI attacks, Cisco finds