authentication

Cloudflare moves up its post-quantum deadline as researchers narrow the path to Q-Day
Cloudflare announced it is targeting 2029 to complete post-quantum security across its entire product suite, including post-quantum authentication. The company is following a …

AI-enabled device code phishing campaign exploits OAuth flow for account takeover
A phishing campaign that bypasses the standard 15-minute expiration window through automation and dynamic code generation, leveraging the OAuth Device Code Authentication flow …
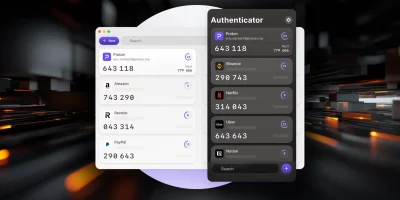
Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app
Proton Authenticator is a free and open-source two-factor authentication (2FA) app that generates time-based one-time passwords (TOTP) to help secure online accounts. It is …

Click, wait, repeat: Digital trust erodes one login at a time
Sign-up forms that drag on, login steps that repeat, and access requests that take longer than expected have become a normal part of using digital services. These moments …

Financial groups lay out a plan to fight AI identity attacks
Generative AI tools have brought the cost of deepfake production low enough that criminals and state-sponsored actors now use them routinely against financial institutions. A …

Microsoft hands Entra ID users new option for MFA
Organizations rely on MFA to enforce identity checks before granting access to systems and services. Microsoft has made external MFA generally available in Microsoft Entra ID, …

Field workers don’t need more access, they need better security
In this Help Net Security interview, Chris Thompson, CISO at West Shore Home, discusses least privilege and credential hygiene for a field-based workforce. He covers access …

Passwords, MFA, and why neither is enough
Passwords weren’t enough, so we added MFA. Now MFA isn’t enough either. In this Help Net Security video, Karlo Zatylny, CTO/CISO at Portnox, walks through why each …

Why workforce identity is still a vulnerability, and what to do about it
Most organizations believe they have workforce identity under control. New hires are verified. Accounts are provisioned. Multi-factor authentication is enforced. Audits are …

One stolen credential is all it takes to compromise everything
Attackers often gain access through routine workflows like email logins, browser sessions, and SaaS integrations. A single stolen credential can give them a quick path to move …

The defense industrial base is a prime target for cyber disruption
Cyber threats against the defense industrial base (DIB) are intensifying, with adversaries shifting from traditional espionage toward operations designed to disrupt production …

Design weaknesses in major password managers enable vault attacks, researchers say
Can cloud-based password managers that claim “zero-knowledge encryption” keep users’ passwords safe even if their encrypted-vault servers are compromised? …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)