passwords

Passwords, MFA, and why neither is enough
Passwords weren’t enough, so we added MFA. Now MFA isn’t enough either. In this Help Net Security video, Karlo Zatylny, CTO/CISO at Portnox, walks through why each …

WhatsApp is adding another lock to your account
Meta has released WhatsApp Beta for Android 2.26.7.8 through the Google Play Beta Program. The update includes references to password-protected accounts, indicating plans to …
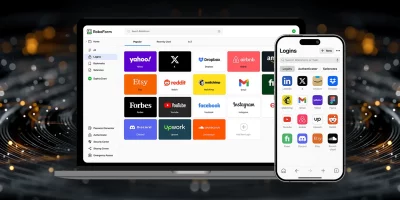
Product showcase: RoboForm password manager for iOS
RoboForm is a password manager that helps users store and manage login credentials, identities, and other sensitive information in one place. The app is available on macOS, …

Password habits are changing, and the data shows how far we’ve come
In this Help Net Security video, Andréanne Bergeron, Security Researcher at Flare, explains how changes in user habits, policy shifts, and new tools have shaped password …

Social data puts user passwords at risk in unexpected ways
Many CISOs already assume that social media creates new openings for password guessing, but new research helps show what that risk looks like in practice. The findings reveal …

The identity mess your customers feel before you do
Customer identity has become one of the most brittle parts of the enterprise security stack. Teams know authentication matters, but organizations keep using methods that …

Is your password manager truly GDPR compliant?
Passwords sit at the core of every critical system, but many organizations still overlook how fragile their password workflows can be. When something goes wrong, security …
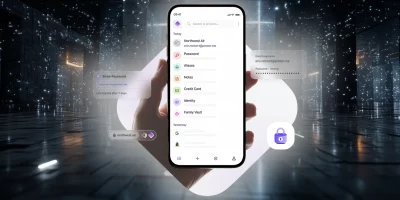
Product showcase: Proton Pass, a password manager with identity protection
Managing passwords can be a real headache, and it’s still common to fall back on reusing them or storing them in a browser without much protection. Proton Pass, built by the …

Employees keep finding new ways around company access controls
AI, SaaS, and personal devices are changing how people get work done, but the tools that protect company systems have not kept up, according to 1Password. Tools like SSO, MDM, …

Passwordless adoption moves from hype to habit
With the average person juggling more than 300 credentials and credential abuse still the top attack vector, the password’s decline is long overdue. Across every major sector, …

For blind people, staying safe online means working around the tools designed to help
Blind and low-vision users face the same password challenges as everyone else, but the tools meant to make security easier often end up getting in the way. A study from the …

The password problem we keep pretending to fix
Experts across industries say they are still losing ground against identity-related breaches, even after years of investment in stronger access controls, according to RSA. …
Featured news
Resources
Don't miss
- Fixing vulnerability data quality requires fixing the architecture first
- ZeroID: Open-source identity platform for autonomous AI agents
- MITRE releases a shared fraud-cyber framework built from real attack data
- Bringing governance and visibility to machine and AI identities
- ClickFix campaign delivers Mac malware via fake Apple page