phishing

Attackers use “Contact Us” forms and fake NDAs to phish industrial manufacturing firms
A recently uncovered phishing campaign – carefully designed to bypass security defenses and avoid detection by its intended victims – is targeting firms in …
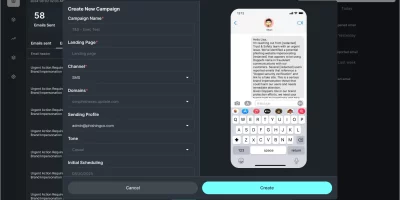
What CISOs can learn from Doppel’s new AI-driven social engineering simulation
Doppel has introduced a new product called Doppel Simulation, which expands its platform for defending against social engineering. The tool uses autonomous AI agents to create …

URL-based threats become a go-to tactic for cybercriminals
Cybercriminals are using advanced social engineering and AI-generated content to make malicious URLs difficult for users to identify, according to Proofpoint. Whether through …

Cybercriminals are getting personal, and it’s working
Cybercriminals are deploying unidentifiable phishing kits (58% of phishing sites) to propagate malicious campaigns at scale, indicating a trend towards custom-made or …

Phishing campaign targets U.S. Department of Education’s G5 portal
A new phishing campaign is targeting users of the U.S. Department of Education’s G5 portal, a site used by educational institutions and vendors to manage grants and federal …
Phishing simulations: What works and what doesn’t
Phishing is one of the oldest and most effective technique used by cybercriminals. No one is immune to them, not even internet security experts, as seen in the case of Troy …

You can’t trust AI chatbots not to serve you phishing pages, malicious downloads, or bad code
Popular AI chatbots powered by large language models (LLMs) often fail to provide accurate information on any topic, but researchers expect threat actors to ramp up their …

ClickFix attacks skyrocketing more than 500%
ClickFix, a deceptive attack method, saw a surge of more than 500% in the first half of 2025, making it the second most common attack vector after phishing, according to …

Using AI to outsmart AI-driven phishing scams
Phishing scams used to be filled with awkward wording and obvious grammar mistakes. Not anymore. AI is now making it harder to distinguish what is real. According to Cofense, …

GitHub becomes go-to platform for malware delivery across Europe
Phishing has become the go-to method for attackers looking to get past security controls and access sensitive environments in Europe, according to Netskope. Users are now …

Microsoft, Dutch security agencies lift veil on Laundry Bear cyber espionage group
The Dutch intelligence and security services have identified a new Russia-affiliated threat group that has been breaching government organizations and commercial entities in …

CTM360 maps out real-time phishing infrastructure targeting corporate banking worldwide
A phishing operation that targets corporate banking accounts across the globe has been analyzed in a new report by CTM360. The campaign uses fake Google ads, advanced …
Featured news
Resources
Don't miss
- Download: Automating Pentest Delivery Guide
- Open-source privacy proxy masks PII before prompts reach external AI services
- cPanel zero-day exploited for months before patch release (CVE-2026-41940)
- Cisco releases open-source toolkit for verifying AI model lineage
- Nine-year-old Linux kernel flaw enables reliable local privilege escalation (CVE-2026-31431)