Features

Your encrypted data is already being stolen
Quantum computing is often treated as a distant, theoretical cybersecurity issue. According to Ronit Ghose, Global Head, Future of Finance of Citi Institute, that mindset is …

Security at AI speed: The new CISO reality
The CISO role has changed significantly over the past decade, but according to John White, EMEA Field CISO, Torq, the most disruptive shift is accountability driven by agentic …

In GitHub’s advisory pipeline, some advisories move faster than others
GitHub Security Advisories are used to distribute vulnerability information in open-source projects and security tools. A new study finds that only a portion of those …

Edge computing’s biggest lie: “We’ll patch it later”
Edge computing is spreading fast, from factory floors to remote infrastructure. But many of these systems are hard to maintain once they are deployed. Devices may run old …

When security decisions come too late, and attackers know it
In this Help Net Security, Chris O’Ferrell, CEO at CodeHunter, talks about why malware keeps succeeding, where attackers insert malicious code in the SDLC, and how CI/CD …

Groupe Rocher CISO on strengthening a modern retail cybersecurity strategy
Global retail and beauty brands manage a unique cybersecurity balancing act. They depend on consumer trust, massive volumes of personal data, and a sprawling network of …

What happens when cybersecurity knowledge walks out the door
In this Help Net Security interview, Andrew Northern, Principal Security Researcher at Censys, explains why mentorship matters and what organizations risk losing when senior …

United Airlines CISO on building resilience when disruption is inevitable
Aviation runs on complex digital systems built for stability, safety, and long lifecycles. That reality creates a unique cybersecurity challenge for airlines, where disruption …

Smart glasses are back, privacy issues included
AI smart glasses are the latest addition to fashion, and they include a camera, a microphone, AI, and privacy risks. After Google Glass failed to gain traction more than a …

When open science meets real-world cybersecurity
Scientific research environments are built for openness and collaboration, often prioritizing long-term discovery over traditional enterprise security. In this Help Net …
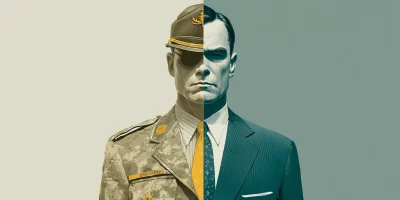
Inside Microsoft’s veteran-to-tech workforce pipeline
The technology workforce is changing, and military veterans are increasingly being recognized as one of the industry’s most valuable and dependable talent pools. In this Help …

One-time SMS links that never expire can expose personal data for years
Online services often treat one-time links sent by text message as low-risk conveniences. A new study shows that these links can expose large amounts of personal data for …
Featured news
Resources
Don't miss
- CISA: Patch actively exploited SolarWinds Serv-U DoS vulnerability (CVE-2026-28318)
- DockSec: Open-source AI-powered Docker security scanner
- Cisco SD-WAN 0-day exploited, no patch available (CVE-2026-20245)
- June 2026 Patch Tuesday forecast: Where are the CVEs?
- AgentGG: Open-source agentic SAST scanner