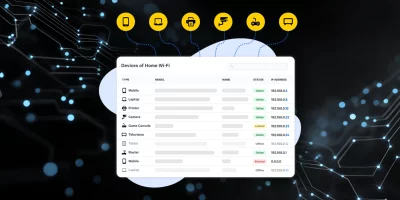
Product Showcase: Fing Desktop puts network visibility on your screen
Phones, laptops, smart TVs, cameras, and smart home equipment all use the same network. Knowing what’s connected helps users manage performance and security. Fing Desktop …

Submarine cables move to the center of critical infrastructure security debate
The cables running along the ocean floor carry the overwhelming majority of the world’s cross-border data traffic, and for most of their operational history they have …

Week in review: Weaponized OAuth redirection logic delivers malware, Patch Tuesday forecast
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: BlacksmithAI: Open-source AI-powered penetration testing framework …

Iran-linked APT targets US critical sectors with new backdoors
An Iran-linked hacking group has been active inside the networks of several US organizations since early February, raising concerns that the activity could precede broader …

Microsoft working on Teams feature to keep unauthorized bots at bay
Microsoft plans to add a new Teams feature that lets meeting admins identify and control third-party bots before they join. According to the Microsoft 365 Roadmap, the feature …

New cyber module strengthens risk planning for health organizations
The Administration for Strategic Preparedness and Response’s (ASPR) new cybersecurity module in the Risk Identification and Site Criticality (RISC) 2.0 Toolkit helps …
Cursor Automations turns code review and ops into background tasks
Cursor Automations, the always-on agent platform from Cursor, is expanding with a new generation of autonomous systems that streamline code review, incident response, and …

OpenAI’s GPT-5.4 doubles down on safety as competition heats up
In the midst of recent developments and controversies surrounding a contract with the U.S. Department of Defense, OpenAI released the GPT-5.4 model. The release comes at a …

March 2026 Patch Tuesday forecast: Is AI security an oxymoron?
Developers and analysts are using more AI tools to produce code and to test both the performance and security of the finished products. They are also embedding AI …

Backup strategies are working, and ransomware gangs are responding with data theft
Business email compromise (BEC) and funds transfer fraud combined for 58% of all cyber insurance claims filed in 2025, according to data from Coalition covering more than …

Why phishing still works today
In this Help Net Security video, Gal Livschitz, Senior Penetration Tester at Terra Security, explains how phishing has evolved and why employees still fall for it. He outlines …

Western governments lay the groundwork for secure 6G networks
Governments are preparing for 6G, the next generation of mobile networks, placing security and resilience among their top priorities. In response, seven countries …