
Cybercrime losses break the $20 billion mark
Online crime continues to generate rising financial losses, with totals reaching $20.877 billion in 2025. The FBI’s Internet Crime Complaint Center (IC3) report shows a 26% …

Russian hackers hijack internet traffic using vulnerable routers
The Russian state cyber group APT28 has been compromising routers to hijack web traffic and spy on victims, the UK’s The National Cyber Security Centre (NCSC) has warned. …

Cloudflare moves up its post-quantum deadline as researchers narrow the path to Q-Day
Cloudflare announced it is targeting 2029 to complete post-quantum security across its entire product suite, including post-quantum authentication. The company is following a …

AI-enabled device code phishing campaign exploits OAuth flow for account takeover
A phishing campaign that bypasses the standard 15-minute expiration window through automation and dynamic code generation, leveraging the OAuth Device Code Authentication flow …

GitHub Copilot CLI gets a second-opinion feature built on cross-model review
Coding agents make decisions in sequence: a plan is drafted, implemented, then tested. Any error introduced early compounds as subsequent steps build on the same flawed …

Comp AI: The open-source way to get compliant with SOC 2, ISO 27001, HIPAA and GDPR
Getting a startup through a SOC 2 audit has long meant months of manual evidence collection, policy writing, and repeated back-and-forth with auditors. A growing number of …

OpenAI opens applications for an external AI safety research fellowship
OpenAI is accepting applications for a paid fellowship program that will fund external researchers to work on safety and alignment questions related to advanced AI systems. …

The case for fixing CWE weakness patterns instead of patching one bug at a time
In this Help Net Security interview, Alec Summers, MITRE CVE/CWE Project Lead, discusses how CWE is moving from a background reference into active use in vulnerability …

How Mimecast brings enterprise-grade email protection to API deployment
In this Help Net Security video, Andrew Williams, Senior Product Manager at Mimecast, walks through the company’s API-based email security protection for Microsoft 365 …

Google study finds LLMs are embedded at every stage of abuse detection
Online platforms are running large language models at every stage of LLM content moderation, from generating training data to auditing their own systems for bias. Researchers …

Residential proxies make a mockery of IP-based defenses
Attack traffic moved through ordinary home and mobile connections in ways that limited the usefulness of IP reputation on its own. GreyNoise observed 4 billion malicious …
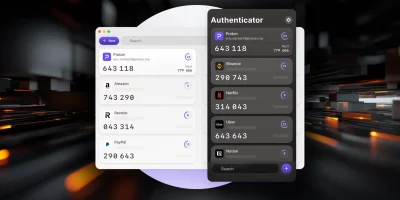
Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app
Proton Authenticator is a free and open-source two-factor authentication (2FA) app that generates time-based one-time passwords (TOTP) to help secure online accounts. It is …
Featured news
Resources
Don't miss
- CISA flags another Cisco Catalyst SD-WAN Manager bug as exploited (CVE-2026-20133)
- A single platform powers SIM farm proxy networks across 17 countries
- Researchers build an encrypted routing layer for private AI inference
- Vercel breached via compromised third-party AI tool
- AI platform ATHR makes voice phishing a one-person job