
Microsoft’s WinUI agent plugin trims token use by over 70% during development
Microsoft published a plugin on May 13 that lets GitHub Copilot CLI and Claude Code drive the full WinUI 3 development cycle, from project scaffolding through signed MSIX …
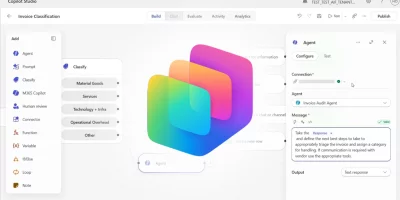
Microsoft turns Copilot Studio into an AI agent control center
The Microsoft Copilot Studio April 2026 updates improve visibility and governance for admins and expand workflow capabilities for managing agents. Copilot surfaces agent …
AI cyber capability is speeding past earlier projections
AI cyber capability is improving faster than expected, with newer models surpassing earlier projections, according to the UK government’s AI Security Institute (AISI). AISI …
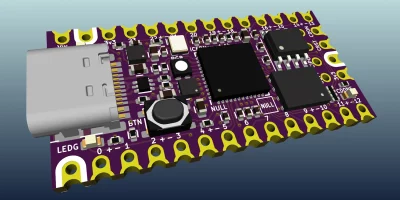
CERN’s open source KiCad library gives the world 17,000 circuit board components
CERN has released its complete KiCad component library under an open source license, making it available to hardware designers anywhere in the world. The library, maintained …
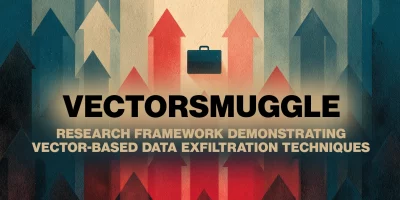
Vector embedding security gap exposes enterprise AI pipelines
Enterprise adoption of retrieval-augmented generation has moved sensitive corporate content into a new storage format that existing security tools cannot inspect. Companies …
Closing the AI governance gap in your enterprise
In this Help Net Security video, Casey Bleeker, CEO at SurePath AI, talks about the AI governance gap that exists in almost every organization. Drawing from three years of …

Over 70% of organizations hit by identity breaches
Attackers rely on stolen credentials, compromised service accounts, and social engineering attacks targeting employees, according to Sophos’ The State of Identity Security …

Machine identities outnumber humans 109 to 1
Organizations manage an average of 109 machine identities for every human identity. AI agents account for a growing share of those identities, with companies expecting AI …
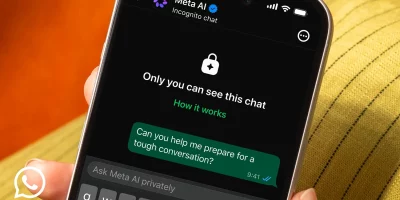
WhatsApp adds Incognito Chat for private Meta AI conversations
The company launched Incognito Chat with Meta AI, a feature that lets users hold AI conversations the platform itself cannot read. The rollout will reach WhatsApp and the …

Signal responds to phishing attacks with new in-app security warnings
Signal is adding new protections for users following recent phishing and social engineering attacks. In March, the FBI and CISA issued a warning stating that Signal had become …
KDE gets over €1 million investment to strengthen security and core infrastructure
European governments and public institutions have been shifting away from proprietary software for years, and the financial infrastructure supporting open-source alternatives …

Microsoft’s agentic security system found four critical Windows RCE flaws
Microsoft responded to growing competition in AI security by announcing that its new agentic security system helped researchers discover 16 new vulnerabilities in the Windows …
Featured news
Resources
Don't miss
- $20 per zero-day is already the WordPress plugin reality
- Deleted Google API keys keep working for up to 23 minutes, researchers warn
- Meet Fractal, an OS made for microarchitecture reverse engineering
- Microsoft open-sources tools for designing and testing AI agents
- GitHub, Grafana Labs breaches traced back to TanStack supply chain compromise