
Google study finds LLMs are embedded at every stage of abuse detection
Online platforms are running large language models at every stage of LLM content moderation, from generating training data to auditing their own systems for bias. Researchers …

Residential proxies make a mockery of IP-based defenses
Attack traffic moved through ordinary home and mobile connections in ways that limited the usefulness of IP reputation on its own. GreyNoise observed 4 billion malicious …
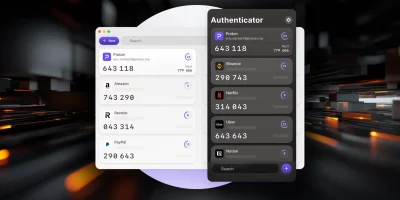
Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app
Proton Authenticator is a free and open-source two-factor authentication (2FA) app that generates time-based one-time passwords (TOTP) to help secure online accounts. It is …

IT talent looks the other way as wireless security incidents pile up
Enterprise wireless networks are supporting a growing mix of devices and applications, increasing operational demand and security exposure. The 2026 Cisco State of Wireless …

CISOs grapple with AI demands within flat budgets
Security spending continues to edge upward across large organizations, though the changes remain gradual and tightly managed. The 2026 RH-ISAC CISO Benchmark reflects a steady …

Week in review: Axios npm supply chain compromise, critical FortiClient EMS bugs exploited
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Financial groups lay out a plan to fight AI identity attacks Generative AI …

FortiClient EMS zero-day exploited, emergency hotfixes available (CVE-2026-35616)
Defused Cyber has spotted a critical Fortinet FortiClient Endpoint Management Server (EMS) zero-day vulnerability (CVE-2026-35616) being exploited in the wild. This time …

Cisco IMC auth bypass vulnerability allows attackers to alter user passwords (CVE-2026-20093)
Cisco has fixed ten vulnerabilities affecting its Integrated Management Controller (IMC), the most critical of which (CVE-2026-20093) could allow an unauthenticated, remote …

Windows Security app gets Secure Boot certificate status indicators as 2026 expiration approaches
Microsoft’s Secure Boot certificates, issued in 2011, are approaching expiration in 2026. To help IT administrators track whether devices have received replacement …

Claude Code source leak exploited to spread malware
A source code leak involving Anthropic’s Claude Code tool quickly escalated into a cybersecurity threat, as attackers seized on the exposed files to lure developers into …

Trivy supply chain attack enabled European Commission cloud breach
CERT-EU confirmed that ShinyHunters are behind the recent breach of the cloud infrastructure underpinning websites of the European Commission, and that they stole and …

Microsoft releases open-source toolkit to govern autonomous AI agents
AI agents can book travel, execute financial transactions, write and run code, and manage infrastructure without human intervention at each step. Frameworks like LangChain, …
Featured news
Resources
Don't miss
- AI adoption is outpacing the safeguards around it
- Agentic AI memory attacks spread across sessions and users, and most organizations aren’t ready
- Review: The Psychology of Information Security
- 29 million leaked secrets in 2025: Why AI agents credentials are out of control
- Hackers hijacked CPUID downloads, served STX RAT to victims