Researchers create DIY IDS for identifying hacked smartphones
A group of researchers from LMG Security has leveraged a Verizon Samsung femtocell – a small cellular station for extending cell phone coverage range indoors or at the cell edge – to create a relatively cheap cellular intrusion detection system that enables enterprises and private individuals to test their or their employees’ smartphones for malware.
“Everyday security professionals and researchers do not have access to inspect cellular network traffic, and therefore cannot detect or respond to mobile malware by deploying network monitoring and intrusion prevention/detection systems, which are commonly used in wireless and Ethernet LANs,” the researchers explained in a white paper.
“Recently, mobile device management (MDM) solutions have grown in popularity, but these solutions are expensive and require control over endpoint devices (especially impractical in BYOD environments).”
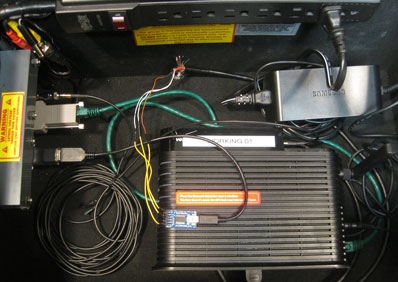
Their solution is much cheaper, and involves the aforementioned femtocell and a Linux-based Snort server through which the traffic to and from the phone is redirected. All in all, they spent less than $300 to set the system up.
In order to test the effectiveness of the setup, they infected a smartphone with the Stels Android Trojan, and have developed custom-written Snort rules to detect it.
“Hacked mobile devices pose extreme risks to confidentiality and information security. Smartphones are carried everywhere: throughout corporations, government agencies, and our nation’s critical infrastructure. Infected mobile devices can intercept text messages, capture location and usage data, and even record surrounding audio,” they pointed out, and said that their goal was to “reverse a critical asymmetry between attack and defense capabilities, and give defenders tools for detecting and preventing mobile malware cheaply and effectively.”
The successfully proved – and demonstrated last week at the Black Hat and Def Con conferences in Las Vegas – that their setup can detected the infection and monitor, stop and alter the data that the infected cell phone sends to the C&C center.
They have also helpfully shared (under a GPL license) the source code that allowed them to do all that, as well as the step-by-step details of their research in a white paper.