Microsoft ends support for Windows 8, IE8 through 10: What does this mean for you?
Slowly but surely, Microsoft is pushing users towards Windows 10 and its new browser, Microsoft Edge.
The way through this is by stop providing technical support and security updates for older versions of the popular OS and the Internet Explorer browser.
On Monday, Microsoft stopped supporting Windows 8 – users are urged to upgrade to Windows 8.1 or Windows 10 (the upgrade is free).
“After January 12, 2016, only the most recent version of Internet Explorer available for a supported operating system will receive technical support and security updates,” the Redmond giant also noted.
The list of operating systems and browser version combinations that will continued to be supported after January 12 looks like this:
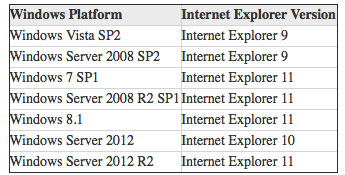
In short, IE7 and IE8 are losing all support, and IE9 and IE10 are only maintained on specific legacy platforms.
“This will make IE maintenance easier for Microsoft, but will create more migration work for IT managers that have to update their browser installations to the latest level. Mid-term this will create a better and more robust platform, but in the short term we are looking at some additional security exposures as legacy browsers will lose their updates,” commented Qualys CTO Wolfgang Kandek.
“So what exactly does EOL mean? No updates, no patches, no fixes, no new versions and no support options if things go wrong. This basically means it’s a hot potato and YOU need to drop it as fast as you can,” Mark James, Security Specialist at ESET, explains. “With the majority of malware being delivered via your web browser these days, it’s imperative you keep it as up-to-date as possible. Of course sometimes it’s not always possible to do this and Microsoft have stated they will do their best to factor in better compatibility into their new Edge browser.”
“But remember as long as you don’t have very special requirements via your own web applications then using one of the other many choices of web browsers that include but are not limited to (in no particular order) Firefox, Chrome or Opera, may be a viable option,” he added.
John Swanciger, CEO at Manta, a large online community for small business owners, advises the following for their community members:
“To dodge security nightmares like malicious cyber attacks that threaten critical business information and data, small businesses need to take action now and get off legacy browsers. With the support cut-off now in effect, businesses need to perform the updates as soon as possible. Most IT departments will be able to painlessly update to IE 11 using the Automatic Updates portal. Those with existing web applications must seek out a Microsoft Certified Partner to figure out which option best fits their organization’s needs and long-term goals. Companies still using old versions of IE are now highly exposed to security issues, so they need to take an all hands on deck approach to immediately roll out fresh browsers.”
“It is safe to assume that cybercriminals have been stockpiling IE vulnerability information ahead of the support cutoff, and they will easily learn new attack techniques for older versions by analyzing future IE 11 updates,” noted Craig Young, security researcher for Tripwire’s Vulnerability and Exposure Research Team (VERT).
Organizations that cannot switch to IE11 by the cutoff date are advised by Tripwire to:
- Ensure all users are running as standard users on Windows browsers, rather than as administrator-level users on their local systems. This will mitigate the risk of many common browser-based malware attacks.
- Businesses with application requirements for older Web browsers should block browsing from vulnerable systems. This step will limit problems that tend to arise during the lunch hour when employees start exploring the Web.
- IT departments should consider deploying network protection rules to drop HTTP requests based on vulnerable user-agent strings. It may be possible for advanced users to change the user-agent string in an attempt to bypass these restrictions, but this step will reduce the attack surface of older browsers.