Remote Butler attack: APT groups’ dream come true
Microsoft security researchers have come up with an extension of the “Evil Maid” attack that allows attackers to bypass local Windows authentication to defeat full disk encryption: “Remote Butler”.
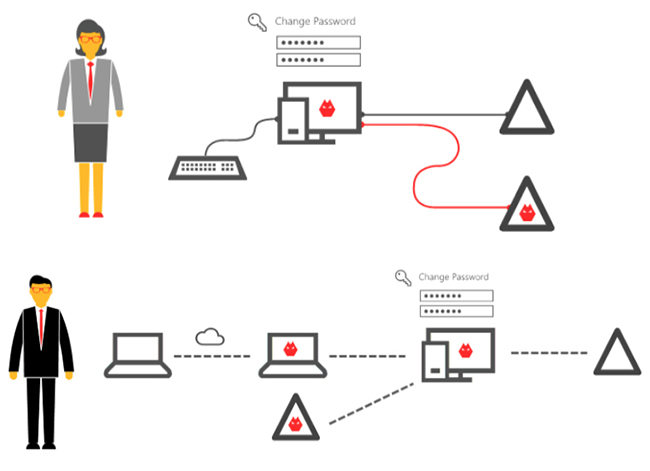
Demonstrated at Black Hat USA 2016 by researchers Tal Be’ery and Chaim Hoch, the Remote Butler attack has one crucial improvement over Evil Maid: it can be effected by attackers who do not have physical access to the target Windows computer that has, at one time, been part of a domain, i.e. enterprise virtual network, and was authenticated to it via a domain controller.
Evil Maid attacks got the name from the fact that even a hotel maid (or someone posing as one) could execute the attack while the computer is left unattended in a hotel room.
The most recent of those was demonstrated by researcher Ian Haken at Black Hat Europe 2015, when he managed to access the target user’s data even when the disk of its computer was encrypted by BitLocker, Windows’ full disk encryption feature.
The vulnerability that allowed this attack was definitely patched by Microsoft in February 2016, and the good news is that this patch also prevents attackers from effecting a “Remote Butler” attack.
But its unlikely that everybody applied the patch.
“While being a clever attack, the physical access requirement for [Haken’s Evil Maid attack] seems to be prohibitive and would prevent it from being used on most APT campaigns. As a result, defenders might not correctly prioritize the importance of patching it,” Be’ery and Hoch explained, and urged those admins who haven’t already implemented it to do so as soon as possible.
Or, if that’s not possible, to implement some network and system hardening and defense-in-depth policy to minimize the risk of the attack being executed.
More technical details about the attack, as well as mitigation options are detailed in this whitepaper.
