Icarus takes control of drones by impersonating their operators
Researcher Jonathan Andersson, a member of Trend Micro’s TippingPoint DVLabs, has demonstrated how a specialized hardware module dubbed Icarus can be used to hijack a variety of widely-used hobbyist drones and make them do your bidding.
Why are such tools necessary
As any technology, flying drones could be put to good use or can be misused to enable crimes and endanger the public and/or individuals. Terror attacks via drones, smuggling contraband into prisons, spying on people – these are just a few examples of (potential) misuse.
Law enforcement, emergency responders, security personnel and others tasked with the safety of individuals and groups are looking into ways to ground these unmanned vehicles without destroying them. Offered solutions and those still being tested vary from point-and-shoot tools that can take control of drones to trained eagles that can take them down.
About Icarus
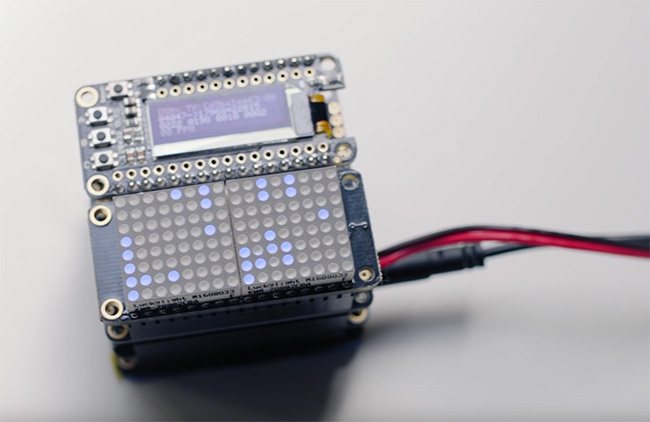
Andersson recently showcased Icarus’ capabilities at the PacSec 2016 security conference in Tokyo.
Those include seizing complete control of drones in range of the device, as well as extracting the drones’ digital fingerprint, so that the owner and his or her motivation for using the drone might be discovered.
Icarus is able to hijack all types of vehicles that use the DSMX remote control protocol, which has been designed and is licensed by Horizon Hobby.
It can discover the unique secret key shared between the vehicle and the operator’s controller by simply observing the (unsecured) protocol, then applying brute-forcing techniques to ferret the key out.
The key is then used to impersonate the operator’s controller – the Icarus operator can use a timing attack vulnerability to transmit orders to the drone just before the real operator does. The drone will accept them as valid and reject those by the legitimate operator.
According to Dan Goodin, Horizon Hobby has declined to offer a comment on this new research. But even if they are willing to work on the issue and remedy this particular problem, not all radio transmitters currently allow the implementation of firmware upgrades.
This state of affairs proves, once again, that introducing security from the very beginning is crucial. Unfortunately, it is too often a victim of manufacturers’ desire for fast development and monetization.
More information about Icarus is included in the video below: