Infosec is a mindset as well as a job, but burnout can happen to anyone
Time and again (and again), survey results tell us that many cybersecurity professionals are close to burnout and are considering quitting their jobs or even leaving the cybersecurity industry entirely.

The reasons for this dire situation vary depending on their role and position within the organization. For example, a recent Ponemon report has revealed that security operations center (SOC) team members are stressed by many things: from increasing workloads, lack of visibility in to the network and IT infrastructure and being on call 24/7/365, to information and alert overload, inability to recruit and retain expert personnel, and lack of resources.
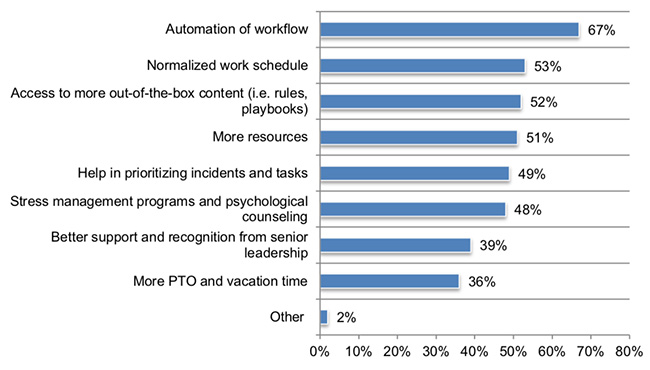
When asked what steps can be taken to alleviate their SOC team’s pain, the pollees’ responses were also wide-ranging (multiple responses were permitted):
In a lively discussion that followed the publication of the report, Joshua Marpet, Chief Operating Officer of Red Lion and long-time tech and security professional, noted that there’s also other things that are getting SOC members down.
“SOC has little career path, very little respect inside or outside the industry, massive responsibilities, not the best pay, and almost no authority to do anything about what they find,” he pointed out.
The problem(s) with the SOC analyst role
“In olden days, being a SOC analyst was a respected gig. Entry-level SOC analyst was how you broke into the industry, learned about alarms, alerts, and notifications, and earned your chops in incident response, root cause analysis, report writing/documentation, and potentially, if you were awesome, in presenting it to the boss(es). Then you were either put on the incident response team, or moved over to digital forensics, or you could maybe switch a bit to DevOps/SecDevOps if that caught your interest. Even pentesting, if you got really good at blue teaming, which is a pretty good pathway into breaking and red teaming,” Marpet explained what he meant to Help Net Security.
“Now, in many companies, SOC analyst is a dead-end job. With the extreme specialization and commoditization of SOC analyst jobs, anything interesting is taken away almost immediately: ‘Oh! This looks bad, send it to Incident Response!’ or ‘I’m not sure what this is, send it to Security!’ SOC analysts became security dispatchers a while ago.”
K.C. Yerrid, an IT security professional who’s no stranger to burnout, also says that it’s difficult to grow from a SOC analyst role in an organization.
“There are six documented causes of burnout: workload, perceived lack of control, insufficient reward, strength of community, fairness, and a values mismatch. Any or all of these can exist and do exist at the SOC Analysts level,” he noted.
“Alert fatigue (workload) is a real phenomenon, and the rate at which alerts can come in could lead to a perceived lack of control in the outcome of one’s responses. We all know that SOC analyst jobs lack sufficient reward, and company culture dictates the strength of community. Finally, as mentioned, it’s an uphill climb to be promoted out of a SOC analyst role. The value mismatch can come from the manager or organizational level.”
A SOC is still a great place to learn all of the above things, but it is generally not a career path starter, Marpet notes.
“If it’s a job you can get, take it – for a year,” he counseled. “Unless you find a great place. I’ve heard that Dave Kennedy’s Binary Defense is a fantastic place. Lots of good places still exist. You just have to find them.”
To SOC analysts who are overworked and close to burning out, he advises thinking hard about the next step.
“If you’re understaffed and overworked due to COVID-19, and it should let up in a month or two, that’s ok. But if your manager is not taking care of you, informing you of what’s happening, if your company has shown no sign of fixing the issue, or set timelines to fix it, why are you there? Go network and find another job. If you have problems doing that, go to CyberSecJobs.com, and check out their listings. If you’re scared of change, hit me up – I do career guidance all the time.”
For those who decide to stay where they are, there’s always the option to try and minimize or remove the stressors that can lead to burnout.
Advice for entering and staying in infosec
To those just entering the information security industry, Marpet advises figuring out who’s the go-to person(s) for the field they want to specialize in – say, digital forensics or pentesting – then finding out when and where they’re speaking.
“Go there, say hello. Don’t gush, don’t beg, don’t cry – just say ‘Hi! Nice to meet you!’ About the fourth time you do this, you’ll see them answering a question you have an opinion on. Mention it. If it’s a good point, you’ll make them think.Then they recognize you from the times you said hi. They know you have a brain. And they know they want to know you.”
Those who still don’t know what they want to concentrate on should go to a conference (when and where possible), meet people, find a village with interesting stuff going on, ask questions, watch and learn.
“Networking is your friend. Meet people. Set up your LinkedIn. People will change their email address, but not their LinkedIn, or MeWe, or whatever is your social network of choice. Say hello and interact with them.”
For staying and thriving in the infosec industry, his best recommendation is to always keep learning: set up a home lab, a development environment, or anything else that will keep you learning everyday.
“Do you know how awesome it is as an interviewer to hear the interviewee get excited about their home lab or new open source tool they just put a commit into or a firewall vuln they figured out? That gets you hired anywhere and everywhere,” he stressed.
Looming infosec industry challenges
Coincidentally, continuous knowledge acquisition is also a way to counteract one of the key challenges the information security industry will have to deal with over the next fixe years: the rising tide of ineptitude.
Colleges are churning out qualified graduates, he says, but many of them are actually not. Infosec has become an overhyped profession, a “sexy” option for those who want to be “cool”. But infosec is a mindset as well as a job, he points out. Most importantly, at the end of the day, you have to be able to do the job.
Other imminent infosec industry challenges? Data security and artificial intelligence that isn’t intelligent.
“Becoming a data-centric business is vital, but most companies have no idea where their data is, what data they own matters, who has rights to that data, and frankly, what security is wrapped around that data,” he noted.
“AI/ML is awesome, fun, and amazing, but if you ask the wrong questions, or don’t ask questions that are broad enough, or targeted enough, you get garbage output. AI does not think for itself (yet), so it can’t tell you how bad an idea your question is – so you have to be careful.”