New infosec products of the week: September 8, 2023
Here’s a look at the most interesting products from the past week, featuring releases from CyberSaint, Ghost Security, Hornetsecurity, NTT Security Holdings, and TXOne Networks.


Reaper: Open-source reconnaissance and attack proxy workflow automation
Reaper is an open-source reconnaissance and attack proxy, built to be a modern, lightweight, and efficient equivalent to Burp Suite/ZAP. It focuses on automation, collaboration, and building universally distributable workflows.


Hornetsecurity releases 365 Total Protection Plan 4 for Microsoft 365 to protect email communications
Hornetsecurity has launched its Plan 4 “Compliance & Awareness” solution of 365 Total Protection Suite, offering a higher level of defence and compliance with new AI tools, security awareness service, and permission management for Microsoft 365. This new plan covers a broader range of an organization’s Microsoft 365 security, compliance management and data protection needs, and prevents existing and potential risks of spam, malware, and threats.


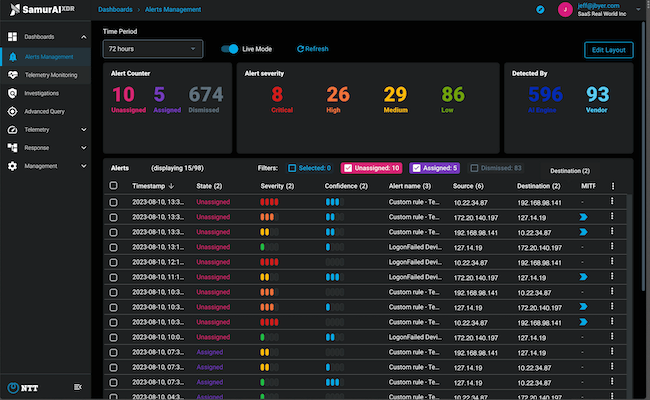
NTT unveils Samurai XDR SaaS to strengthen detection and response capabilities across the network
Samurai XDR gives users visibility and control across network, endpoint, cloud, email and more through an intuitive interface. With no long-term contracts, Samurai XDR SaaS combines the power of NTT’s enterprise-grade technology with the flexibility and affordability SMBs need to protect against modern cyber threats.

CyberSaint launches Remediation Suite to optimize resource allocation and decision-making
CyberSaint has launched the Remediation Suite within the CyberStrong platform. With the Remediation Suite, CISOs and cyber risk professionals gain access to a toolkit to efficiently prioritize, quantify, track and communicate remediation efforts across controls and risks, leading to optimized resource allocation and informed decision-making.


TXOne Networks Edge V2 isolates security breaches
Edge V2 is equipped with operation-oriented OT network visibility design and an advanced OT-intelligent policy deployment mechanism. The solution also delivers inline virtual patching for proactive protection from vulnerabilities without operational downtime, form-factor flexibility for building a defense-in-depth posture and deep analysis across a tremendous range of network protocols.

