Anamarija Pogorelec

Measuring AI use becomes a business requirement
Enterprise teams already run dozens of AI tools across daily work. Usage stretches from code generation and analytics to customer support drafting and internal research. …

Auto finance fraud is costing dealers up to $20,000 per incident
Auto retailers see fraud as a regular part of selling and financing vehicles, something that shows up often enough to plan around, according to Experian. Income and identity …

Sandisk brings SPRandom to open source for large SSD testing
Enterprise storage environments already run long qualification cycles as solid-state drive capacities rise and validation teams try to mirror production workloads. …
OpenAI releases Codex macOS app for agent-based software development
OpenAI has launched the new Codex app for macOS, a dedicated workspace for managing multiple AI coding agents in parallel. The app is designed to help developers reduce …

Open-source attacks move through normal development workflows
Software development relies on a steady flow of third-party code, automated updates, and fast release cycles. That environment has made the software supply chain a routine …
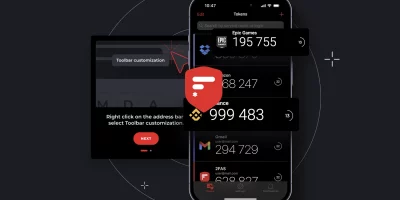
Product showcase: 2FAS Auth – Free, open-source 2FA for iOS
Online accounts usually rely on a password, but passwords alone can be weak if they’re reused, easily guessed, or stolen. Two-factor authentication (2FA) adds a second layer …

Cybersecurity jobs available right now: February 3, 2026
Application Security Engineer Liebherr Group | Germany | Hybrid – View job details As an Application Security Engineer, you will As an Application Security Engineer, you …

AI is flooding IAM systems with new identities
Most organizations view AI identities through the same lens used for other non-human identities, such as service accounts, API keys, and chatbots, according to The State of …

Apple’s new privacy feature limits how precisely carriers track your location
Apple users are already accustomed to managing app-level location permissions, and a new privacy feature in iOS 26.3 extends that control to cellular networks. Called Limit …

Security teams are carrying more tools with less confidence
Enterprise environments now span multiple clouds, on-premises systems, and a steady flow of new applications. Hybrid and multi-cloud setups are common across large …

New infosec products of the month: January 2026
Here’s a look at the most interesting products from the past month, featuring releases from Acronis, Booz Allen Hamilton, cside, Descope, JumpCloud, MIND, Noction, Obsidian …

Open-source malware zeroes in on developer environments
Open source malware activity during 2025 concentrated on a single objective: executing code inside developer environments, according to Sonatype. The focus reflected a broader …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)