authentication

Product showcase: Ente Auth encrypts, backs up, and syncs 2FA
Two-factor authentication (2FA) is an essential layer of protection for online accounts, and Ente Auth makes it easier to manage securely across devices. Ente Auth is a free, …

29 million leaked secrets in 2025: Why AI agents credentials are out of control
AI agents need credentials to work. They authenticate with LLM platforms, connect to databases, call SaaS APIs, access cloud resources, and orchestrate across dozens of …

Cloudflare moves up its post-quantum deadline as researchers narrow the path to Q-Day
Cloudflare announced it is targeting 2029 to complete post-quantum security across its entire product suite, including post-quantum authentication. The company is following a …

AI-enabled device code phishing campaign exploits OAuth flow for account takeover
A phishing campaign that bypasses the standard 15-minute expiration window through automation and dynamic code generation, leveraging the OAuth Device Code Authentication flow …
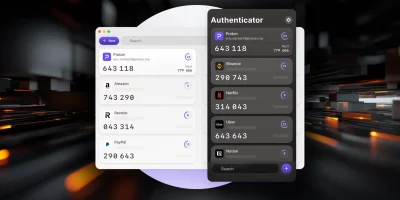
Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app
Proton Authenticator is a free and open-source two-factor authentication (2FA) app that generates time-based one-time passwords (TOTP) to help secure online accounts. It is …

Click, wait, repeat: Digital trust erodes one login at a time
Sign-up forms that drag on, login steps that repeat, and access requests that take longer than expected have become a normal part of using digital services. These moments …

Financial groups lay out a plan to fight AI identity attacks
Generative AI tools have brought the cost of deepfake production low enough that criminals and state-sponsored actors now use them routinely against financial institutions. A …

Microsoft hands Entra ID users new option for MFA
Organizations rely on MFA to enforce identity checks before granting access to systems and services. Microsoft has made external MFA generally available in Microsoft Entra ID, …

Field workers don’t need more access, they need better security
In this Help Net Security interview, Chris Thompson, CISO at West Shore Home, discusses least privilege and credential hygiene for a field-based workforce. He covers access …

Passwords, MFA, and why neither is enough
Passwords weren’t enough, so we added MFA. Now MFA isn’t enough either. In this Help Net Security video, Karlo Zatylny, CTO/CISO at Portnox, walks through why each …

Why workforce identity is still a vulnerability, and what to do about it
Most organizations believe they have workforce identity under control. New hires are verified. Accounts are provisioned. Multi-factor authentication is enforced. Audits are …

One stolen credential is all it takes to compromise everything
Attackers often gain access through routine workflows like email logins, browser sessions, and SaaS integrations. A single stolen credential can give them a quick path to move …
Featured news
Resources
Don't miss
- Dutch police disrupts botnet composed of 17 million devices
- New infostealer reaches enterprise devices through FortiClient EMS vulnerability
- LinkedIn-themed phishing abuses Adobe’s A/B testing platform
- The behavioral signals that sharpen Trojan malware detection
- Zapier exploit chain shows how known anti-patterns compose into critical risk