cybersecurity

Meta turns to AI to sniff out scams on Facebook, Messenger and WhatsApp
Meta’s new tools on Facebook, Messenger, and WhatsApp protect users from scams. They use advanced AI systems to analyze text, images, and surrounding context and identify …

Zero trust, zero buzzwords: Here’s what it means
In this Help Net Security video, Murat Balaban, CEO of Zenarmor, breaks down zero trust and zero trust network access (ZTNA) without the buzzwords. The video covers why this …

Software vulnerabilities push credential abuse aside in cloud intrusions
Cloud intrusions are unfolding on shorter timelines, with attackers leaning more on unpatched software and compromised identities. H2 2025 distribution of initial access …

Airbus CSO on supply chain blind spots, space threats, and the limits of AI red-teaming
Pascal Andrei, CSO at Airbus, knows that the aerospace and defense sector is facing a threat environment that is evolving faster than most organizations can track. From …

The people behind cyber extortion are often in their forties
Many cybercrime investigations end with arrests or indictments that reveal little about the people behind the operations. When authorities do disclose demographic details, the …

Bug bounties are broken, and the best security pros are moving on
Penetration testing engagements are organized as scheduled contracts with defined scope, set testing windows, and direct communication channels with client teams. Cobalt’s …

No more soft play, President Trump warns in new cyber strategy
The White House released “President Trump’s Cyber Strategy for America,” a policy framework outlining the administration’s priorities for maintaining U.S. leadership in …

More AI tools, more burnout! New research explains why
Workflows built around multiple AI agents and constant tool switching are adding cognitive strain across large enterprises. A recent Harvard Business Review analysis describes …

OpenAI joins the race in AI-assisted code security
OpenAI introduced Codex Security, an AI agent that reviews codebases to find, verify, and help fix software vulnerabilities. The launch comes a few weeks after rival …

Decoding silence: How deaf and hard-of-hearing pros are breaking into cybersecurity
Stu Hirst was already a CISO when he started to go deaf. It was 2023, and the hearing loss crept in over months, enough for him to adapt, to lean on hearing aids and captions, …

Open-source tool Sage puts a security layer between AI agents and the OS
Autonomous AI agents running on developer workstations execute shell commands, fetch URLs, and write files with little or no inspection of what they are doing. Open-source …
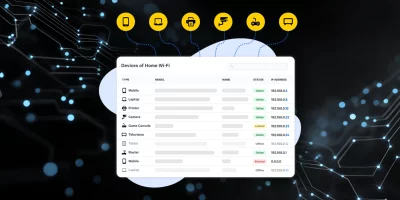
Product showcase: Fing Desktop puts network visibility on your screen
Phones, laptops, smart TVs, cameras, and smart home equipment all use the same network. Knowing what’s connected helps users manage performance and security. Fing Desktop …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)