open source

Social engineering attacks on open source developers are escalating
North Korean hackers spent weeks socially engineering an Axios maintainer through a fake Slack workspace, a cloned company identity, and a fabricated Microsoft Teams call that …

Comp AI: The open-source way to get compliant with SOC 2, ISO 27001, HIPAA and GDPR
Getting a startup through a SOC 2 audit has long meant months of manual evidence collection, policy writing, and repeated back-and-forth with auditors. A growing number of …
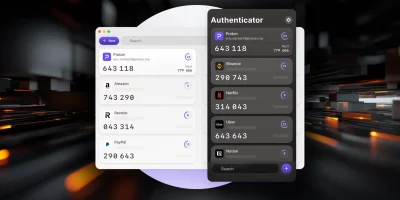
Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app
Proton Authenticator is a free and open-source two-factor authentication (2FA) app that generates time-based one-time passwords (TOTP) to help secure online accounts. It is …

Microsoft releases open-source toolkit to govern autonomous AI agents
AI agents can book travel, execute financial transactions, write and run code, and manage infrastructure without human intervention at each step. Frameworks like LangChain, …

OpenSSH 10.3 patches five security bugs and drops legacy rekeying support
OpenSSH 10.3 shipped carrying five security fixes alongside feature additions and a set of behavior changes that will break compatibility with older SSH implementations that …

Intel puts its data center performance knowledge on GitHub
Intel engineers have published a centralized repository of data center performance knowledge on GitHub, giving practitioners direct access to tuning guides, configuration …

Rspamd 4.0.0 ships memory savings, a new scan protocol, and a required migration step
The open-source spam filtering platform Rspamd released version 4.0.0, delivering infrastructure changes across its scan protocol, memory model, hash storage, and …

Hottest cybersecurity open-source tools of the month: March 2026
Presented here is a curated selection of noteworthy open-source cybersecurity solutions that have drawn recognition for their ability to enhance security postures across …

SystemRescue 13 updates its kernel to Linux 6.18 LTS, adds new recovery tools
Bootable Linux recovery environments occupy a specific niche in the systems administration and incident response toolkit. SystemRescue, an Arch-based live distribution built …

ShipSec Studio brings open-source workflow orchestration to security operations
Security teams have long relied on a mix of shell scripts, cron jobs, and loosely connected tools to chain reconnaissance and vulnerability scanning work together. ShipSec …

TeamPCP strikes again: Backdoored Telnyx PyPI package delivers malware
TeamPCP continues is supply chain compromise rampage, with telnyx on PyPI being the latest maliciously modified package. What happened? Telnyx is a widely used software …

Tails 7.6 ships automatic Tor bridge retrieval and a new password manager
Tails 7.6 is out, and for users operating on networks that block Tor, the most consequential addition is built-in bridge retrieval. The Tor Connection assistant can now detect …
Featured news
Resources
Don't miss
- Dutch police disrupts botnet composed of 17 million devices
- New infostealer reaches enterprise devices through FortiClient EMS vulnerability
- LinkedIn-themed phishing abuses Adobe’s A/B testing platform
- The behavioral signals that sharpen Trojan malware detection
- Zapier exploit chain shows how known anti-patterns compose into critical risk