software
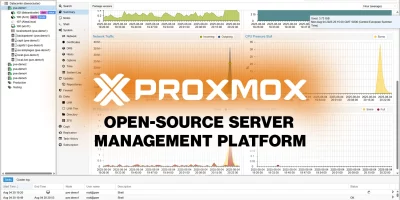
Open-source server management platform Proxmox VE 9.0 released
Proxmox Virtual Environment (VE) 9.0 introduces advancements in both storage and networking capabilities, addressing critical enterprise demands. A highlight is the …

BloodHound 8.0 debuts with major upgrades in attack path management
SpecterOps has released BloodHound 8.0, the latest iteration of its open-source attack path management platform, featuring major enhancements and expanded capabilities. …

Open-source password recovery utility Hashcat 7.0.0 released
Hashcat is an open-source password recovery tool that supports five attack modes and more than 300 highly optimized hashing algorithms. It runs on CPUs, GPUs, and other …
Artemis: Open-source modular vulnerability scanner
Artemis is an open-source modular vulnerability scanner that checks different aspects of a website’s security and translates the results into easy-to-understand messages that …
Vulnhuntr: Open-source tool to identify remotely exploitable vulnerabilities
Vulnhuntr is an open-source tool that finds remotely exploitable vulnerabilities. It uses LLMs and static code analysis to trace how data moves through an application, from …
Autoswagger: Open-source tool to expose hidden API authorization flaws
Autoswagger is a free, open-source tool that scans OpenAPI-documented APIs for broken authorization vulnerabilities. These flaws are still common, even at large enterprises …

Cervantes: Open-source, collaborative platform for pentesters and red teams
Cervantes is an open-source collaborative platform built for pentesters and red teams. It offers a centralized workspace to manage projects, clients, vulnerabilities, and …

Calico: Open-source solution for Kubernetes networking, security, and observability
Calico is an open-source unified platform that brings together networking, security, and observability for Kubernetes, whether you’re running in the cloud, on-premises, …

Review: Passwork 7.0, self-hosted password manager for business
Over the years, the number of services we use has exploded, and so has the need to protect our credentials. Back in what I like to call “the age of innocence,” we scribbled …

Falco: Open-source cloud-native runtime security tool for Linux
Falco is an open-source runtime security tool for Linux systems, built for cloud-native environments. It monitors the system in real time to spot unusual activity and possible …

pqcscan: Open-source post-quantum cryptography scanner
pqcscan is an open-source tool that lets users scan SSH and TLS servers to see which Post-Quantum Cryptography (PQC) algorithms they claim to support. It saves the results in …

Kanvas: Open-source incident response case management tool
Kanvas is an open-source incident response case management tool with a simple desktop interface, built in Python. It gives investigators a place to work with SOD (Spreadsheet …