
Singapore telcos breached in China-linked cyber espionage campaign
Singapore’s four major telecommunications companies were hit by a coordinated cyber espionage campaign last year, the country’s Cyber Security Agency (CSA) has revealed. …

Microsoft tightens Windows security with app transparency and user consent
Microsoft is strengthening default protections in Windows through two security initiatives, Windows Baseline Security Mode and User Transparency and Consent. User Transparency …

Trojanized 7-Zip downloads turn home computers into proxy nodes
A trojanized version of the popular 7-Zip software is quietly turning home computers into residential proxy nodes, Malwarebytes warns. Spurred by a Reddit post in which a user …

Unpatched SolarWinds WHD instances under active attack
Internet‑exposed and vulnerable SolarWinds Web Help Desk (WHD) instances are under attack by threat actors looking to gain an initial foothold into target organizations’ …
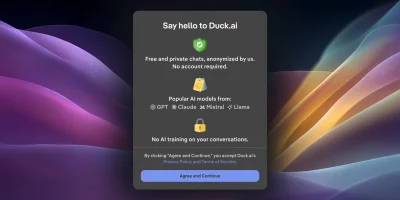
DuckDuckGo enables AI voice chat without saving voice data
DuckDuckGo has added voice chat to Duck.ai, allowing users to speak to an AI assistant while keeping audio private, unrecorded, and excluded from AI training. Voice chat is …

How AI is reshaping attack path analysis
Cybersecurity teams are overwhelmed with data and short on clarity, while adversaries use AI to move faster and operate at unprecedented scale. Most organizations collect …

Face scans and ID checks are coming to Discord
Discord users will soon see a change to how their accounts work. From early March 2026, access to some features will require age verification using an ID or a face scan. The …

What happens when cybersecurity knowledge walks out the door
In this Help Net Security interview, Andrew Northern, Principal Security Researcher at Censys, explains why mentorship matters and what organizations risk losing when senior …

AI-driven scams are eroding trust in calls, messages, and meetings
In this Help Net Security video, Miguel Fornés, Governance and Compliance Manager at Surfshark, discusses how AI is changing social engineering attacks. He describes how tasks …

Cybersecurity jobs available right now: February 10, 2026
Cloud Security Engineer KPMG | Israel | On-site – No longer accepting applications As a Cloud Security Engineer, you will establish, secure, and support critical Azure …

Ransomware group breached SmarterTools via flaw in its SmarterMail deployment
SmarterTools, the company behind the popular Microsoft Exchange alternative SmarterMail, has been breached by a ransomware-wielding group that leveraged a recently fixed …

European Commission hit by cyberattackers targeting mobile management platform
The European Commission’s mobile device management platform was hacked but the incident was swiftly contained and no compromise of mobile devices was detected, …
Featured news
Resources
Don't miss
- Social engineering attacks on open source developers are escalating
- Chaos malware expands from routers to Linux cloud servers
- What managing partners should ask AI vendors before signing any contract
- Anthropic’s new AI model finds and exploits zero-days across every major OS and browser
- Comp AI: The open-source way to get compliant with SOC 2, ISO 27001, HIPAA and GDPR